Securin Zero-Days
CVE-2020-29324 - D-Link Router DIR-895L MFC Telnet Hardcoded Credentials
Description
The DLink Router DIR-895L MFC v1.21b05 is vulnerable to credentials disclosure in telnet service through decompilation of firmware, that allows an unauthenticated attacker to gain access to the firmware and to extract sensitive data.
Proof of Concept (POC):
Issues: The telnet hardcoded default credentials are the vulnerable elements in the firmware of DIR-868L.
Step 1: Extract the firmware
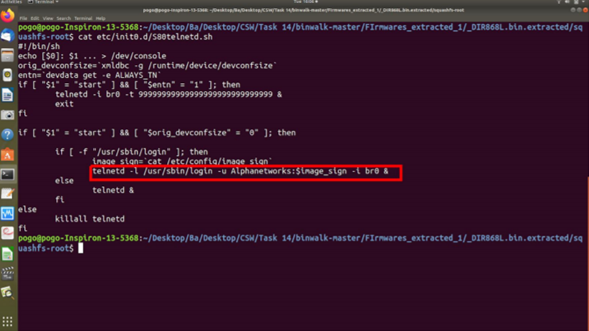
Step 2: Run the command cat etc/init0.d/S80telnetd.sh to get the username and the location of the variable used for storing the password.
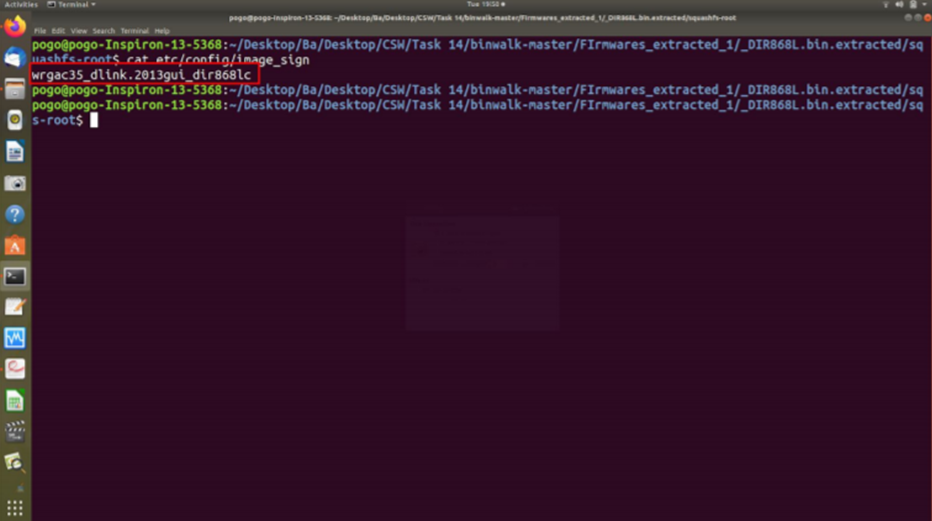
Step 3: Run the command cat etc/config/image_sign to get the password
Impact
A successful exploit could allow the attacker to gain access to the firmware and to extract sensitive data.
Remediations
D-Link released a support announcement in response to the recommendations provided by CSW team for these D-Link products – https://supportannouncement.us.dlink.com/announcement/publication.aspx?name=SAP10189
Timeline