Securin Zero-Days
CVE-2020-14445 - Stored Cross-Site Scripting in WSO2 Product
Description
A cross-site scripting (XSS) attack can cause arbitrary code (JavaScript) to run in a user’s browser while the browser is connected to a trusted web site. The application targets your users and not the application itself, but it uses your application as the vehicle for the attack. XSS payload is executed when the user loads a page created in WSO2 Identity Server version 5.9.0 Product.
*Affected Products: WSO2 IS as Key Manager 5.9.0 or earlier, WSO2 Identity Server 5.9.0 or earlier
Proof of Concept (POC):
The following vulnerability was tested on WSO2 Identity Server version 5.9.0 Product.
Issue 1: Stored cross-site scripting.
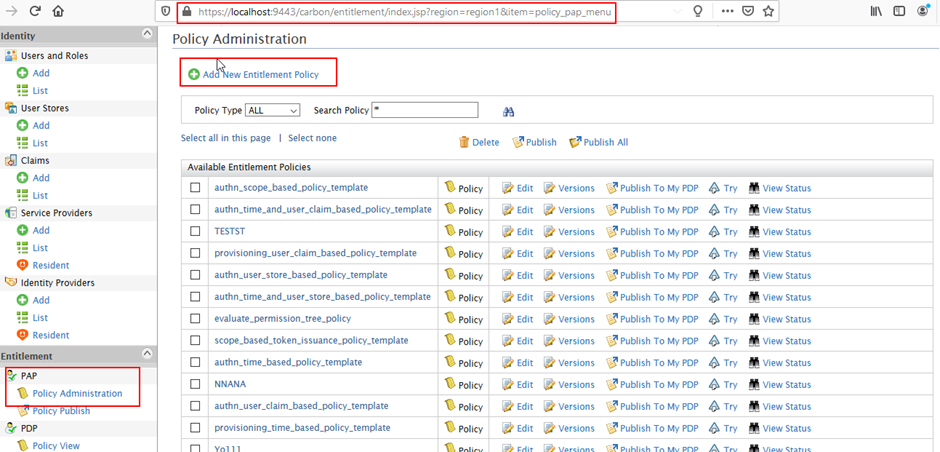
Figure 1: Navigating to the Policy Administration and Clicking the Add New Entitlement Policy Link.
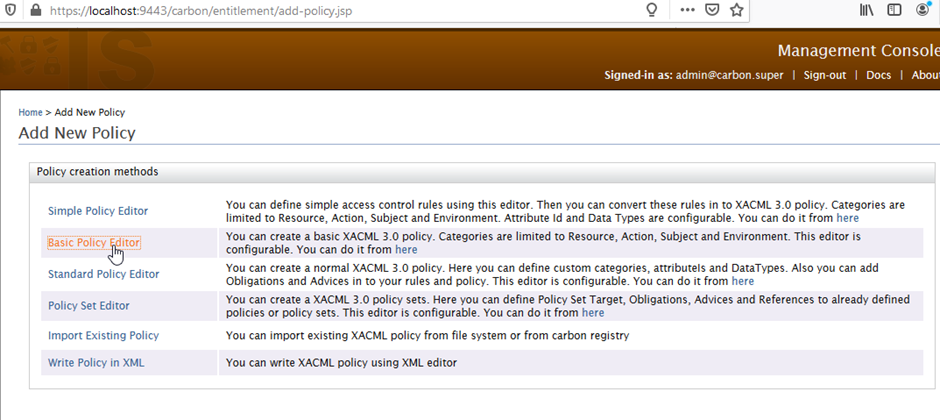
Figure 2: Clicking on Basic Policy Editor will redirect to the URL.
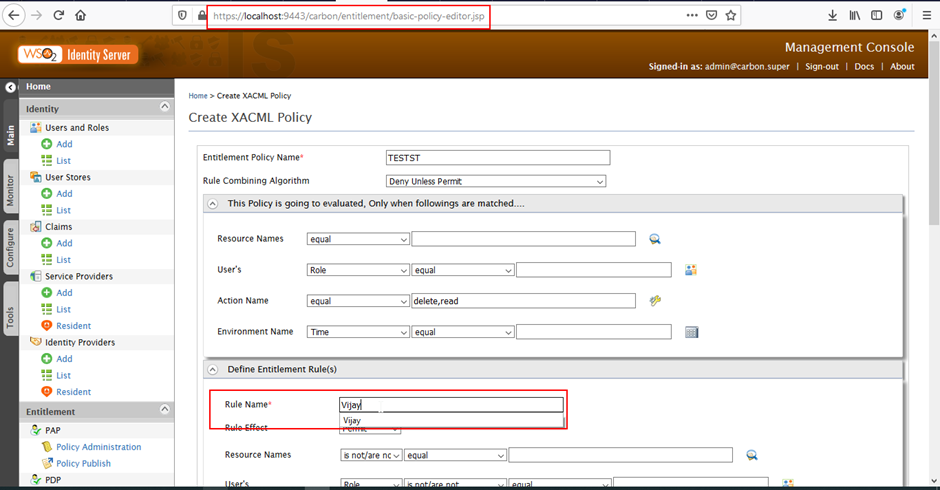
Figure 3: Fill the necessary details and Move to the Define Entitlement Rules section.
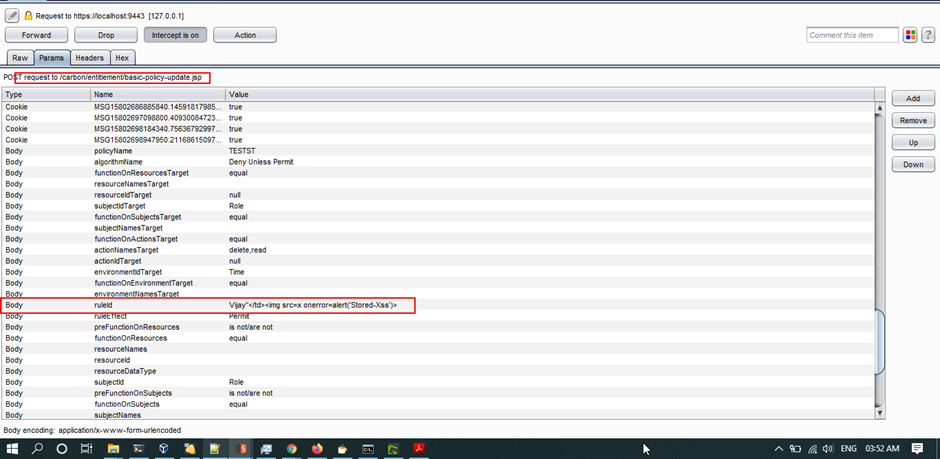
Figure 4: Intercepting the request, and ‘RuleID’ variable is added with XSS Payload.
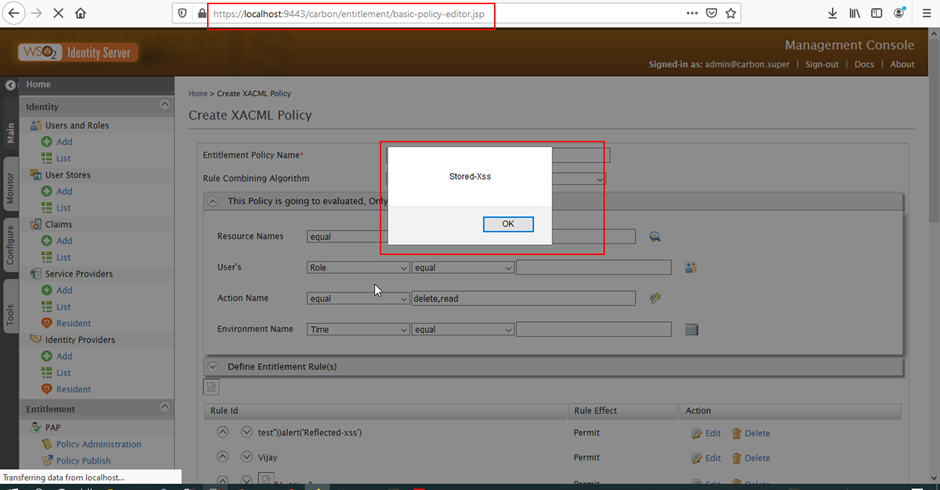
Figure 5: Inserted payload gets stored and executed whenever the user visits the page.
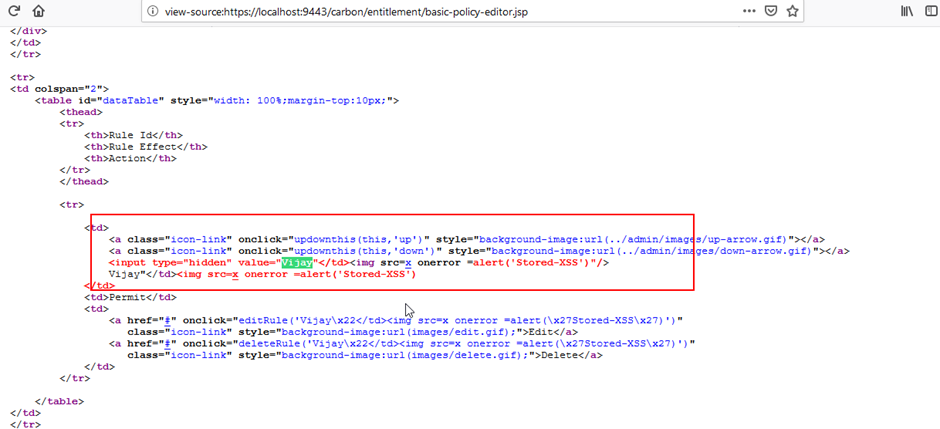
Figure 6: Stored XSS payload in the source code.
Impact
By leveraging an XSS attack, an attacker can make the browser get redirected to a malicious website, make changes in the UI of the web page, retrieve information from the browser or harm otherwise. However, since all the session related sensitive cookies are set with httpOnly flag and protected, session hijacking or similar attacks would not be possible.
Remediations
Apply the relevant fixes based on the changes from the public fix using the following link:
Timeline