Securin Zero-Days
CVE-2019-20439 - Reflected Cross-Site Scripting in WSO2
Description
A vulnerability was discovered on WSO2 API Manager 2.6.0 in defining the scope to manage the API page of the API Publisher. An input variable vulnerable to stored XSS is ‘roles’ on the API page. A reflected cross-site script (XSS) vulnerability allows an attacker to inject malicious code into the scope to an API in the API publisher by providing XSS payload as a value for roles.
Proof of Concept (POC):
The following vulnerability was tested on the WSO2 API Manager version 2.6.0 Product.
Issue 01: Reflected Cross-Site Scripting.
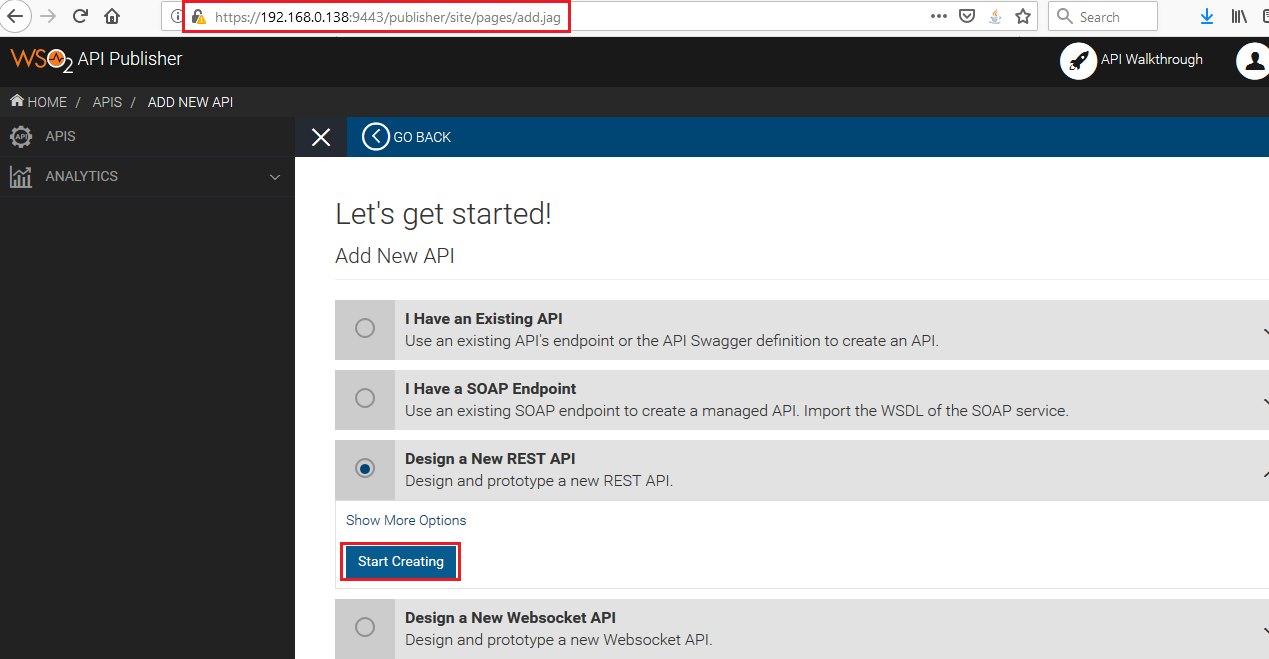
Figure 01: Start creating an API.
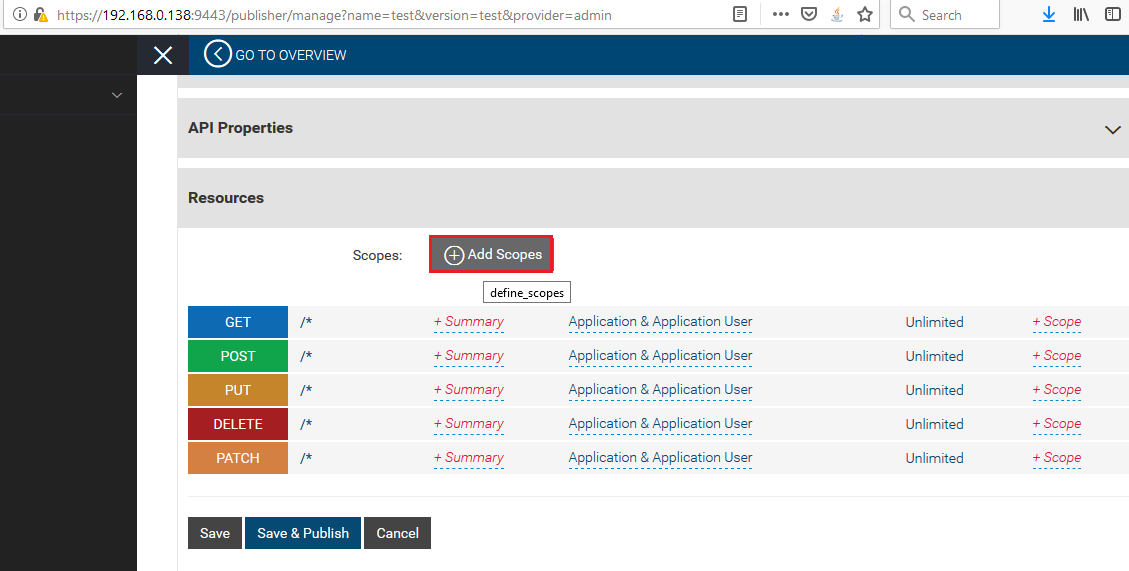
Figure 02: Click on the Add Scope button to add resources information.
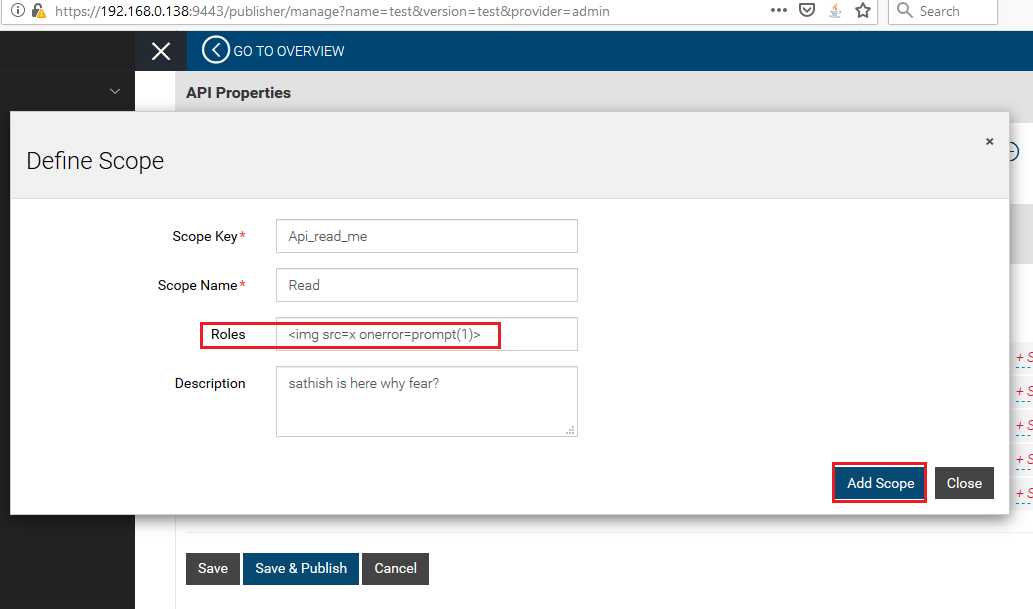
Figure 03: Enter XSS Payload the Roles section.
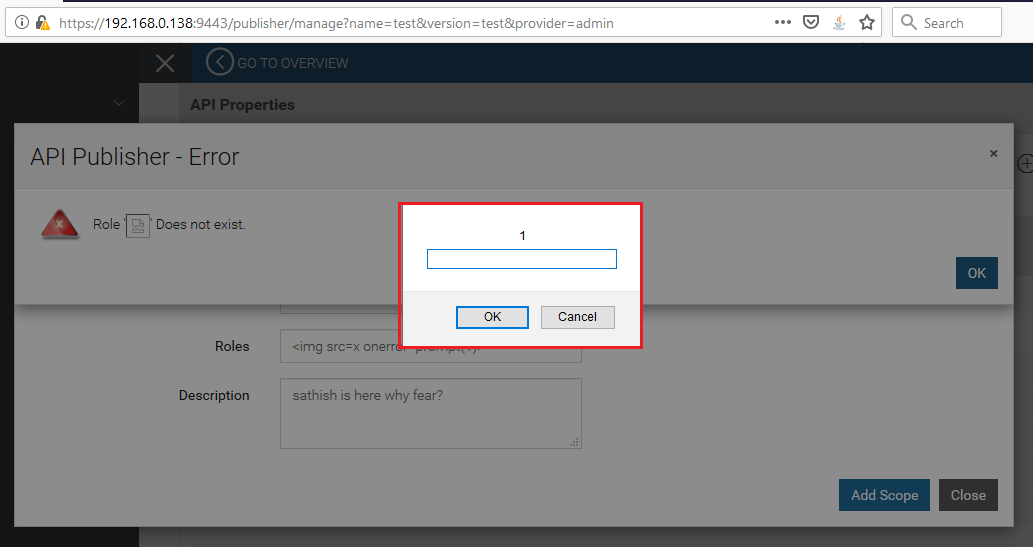
Figure 04: Injected XSS payload, <img src=x onerror=prompt(1)> gets reflected in the same browser as response.
Impact
Through an XSS attack, the attacker can make the browser redirect to a malicious website. Unauthorized actions such as changing the UI of the web page, retrieving information from the browser are possible. But since all session-related sensitive cookies are set with httpOnly flat and protected, session hijacking or mounting a similar attack would not be possible.
Remediations
Download the relevant patch based on the product version.
Code | Product | Version | Patch |
AM | WSO2 API Manager | 2.6.0 |
Timeline