Securin Zero-Days
CVE-2019-20435 - Reflected Cross-Site Scripting in WSO2 Product
Description
A vulnerability was discovered on WSO2 products inline API documentation editor page of the API Publisher. A reflected cross-site script (XSS) vulnerability allows an attacker to perform in the inline API documentation editor page of the API Publisher by sending an HTTP GET request with a harmful request parameter for ‘docName.’
Proof of Concept (POC):
The POST request docName variable is vulnerable to reflected Cross-Site Scripting (XSS) in the URL, https://192.168.107.2:9443/publisher/site/blocks/documentation/ajax/docs.jag
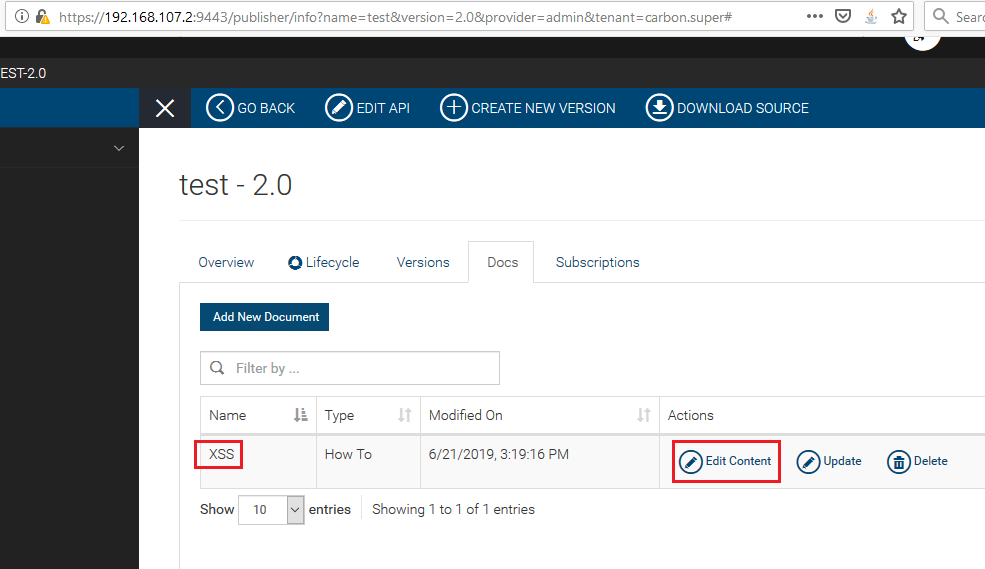
Figure 01: New document created in the API.
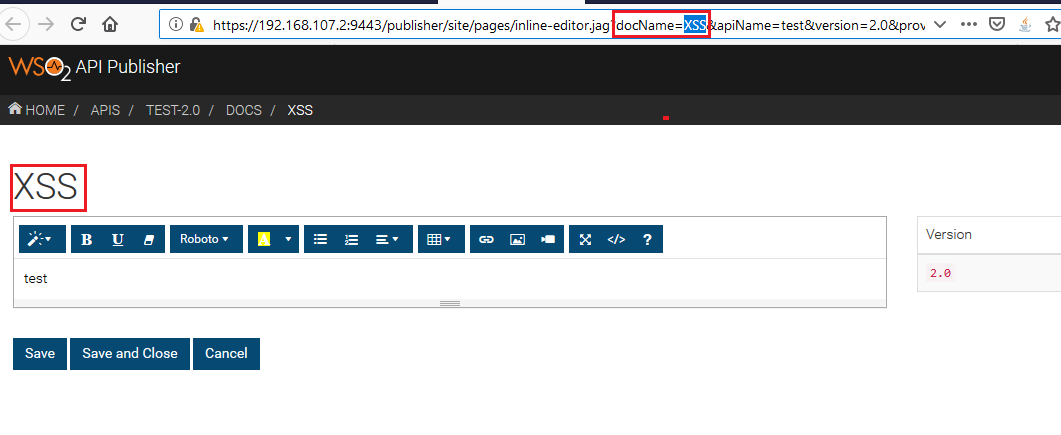
Figure 02: Choose ‘Edit Content’ to edit document information.
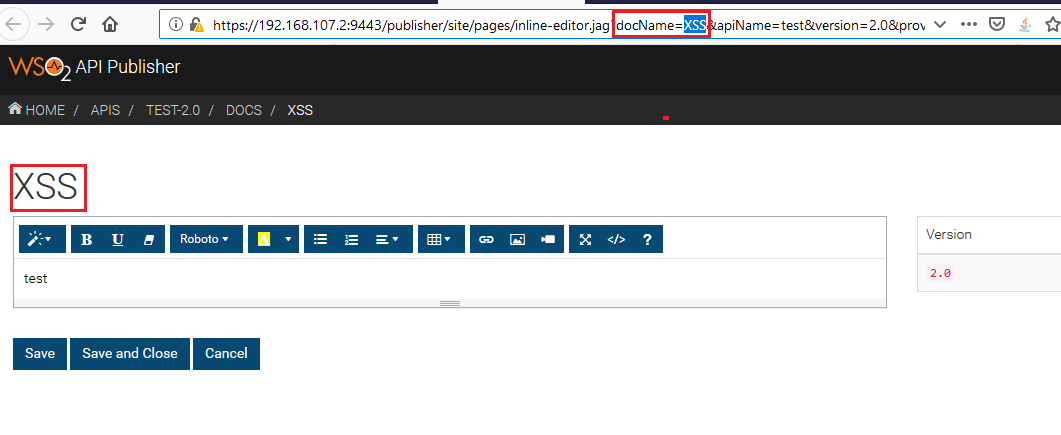
Figure 03: Actual GET request URL.
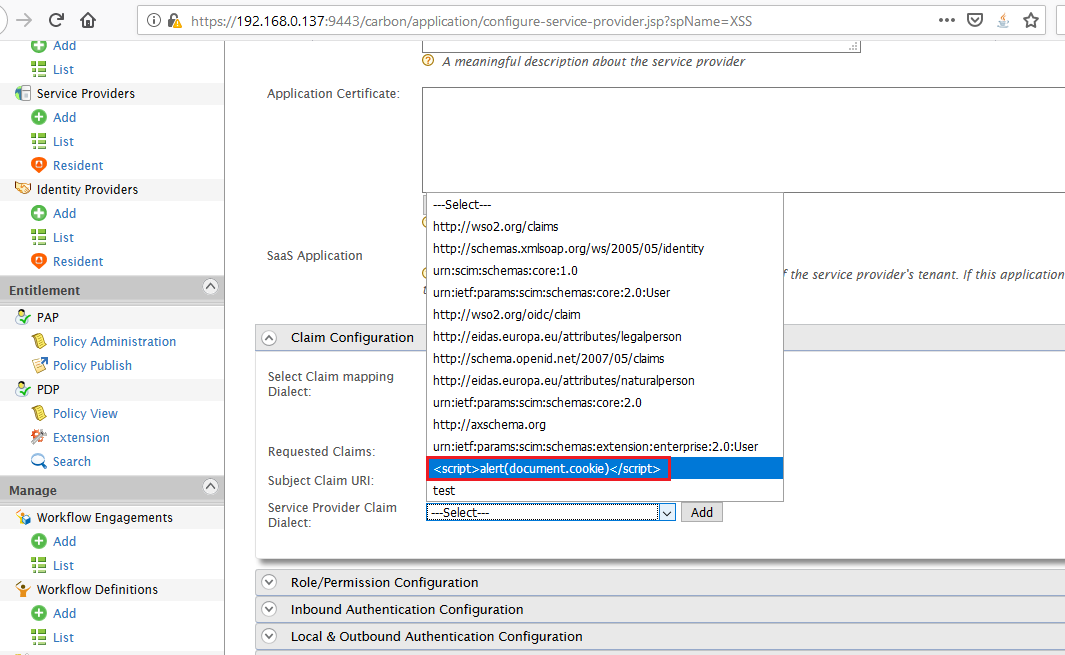
Figure 04: Crafted request with XSS payload, XSS<img src=x onerror=prompt(1)> gets reflected in the same browser as response.
Impact
By tricking a privileged user into clicking a created URL via email, IM, or a neutral web site, the attacker can make the browser get redirected to a malicious website, which makes changes in the UI of the web page and retrieve information from the browser or harm otherwise. But since all session-related sensitive cookies are set with httpOnly flat and protected, session hijacking or mounting a similar attack would not be possible.
Remediations
Download the relevant patch based on the product version.
Code | Product | Version | Patch |
AM | WSO2 API Manager | 2.6.0 |
Timeline