Securin Zero-Days
CVE-2019-20365 - Multiple Reflected Cross-Site Scripting in Openfire Product
Description
A cross-site scripting (XSS) attack can cause arbitrary code (javascript) to run in a user’s browser while the browser is connected to a trusted web site. The application targets your application’s users and not the application itself, but it uses your application as the vehicle for the attack. XSS payload is executed whenever the user submits the crafted POST request with XSS Payload in Openfire 4.4.4 Product.
Proof of Concept (POC):
The following vulnerability was tested on Openfire version 4.4.4 Product.
The following vulnerability was tested on Openfire version 4.4.4 Product.
Issue 01: The GET Request “search” variable in the URL http://localhost:9090/user-groups.jsp?search=test&username=admin is failing to validate XSS payload in the client-side, which results in reflected cross-site scripting.
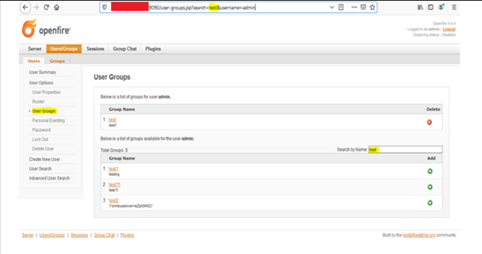
Figure 01: Groups name is searching with the help Search by name button. (here the search is ‘reflected XSS’).
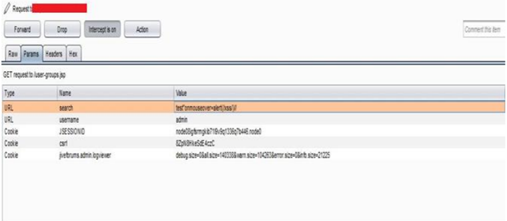
Figure 02: Add XSS payload to the variable “search.”
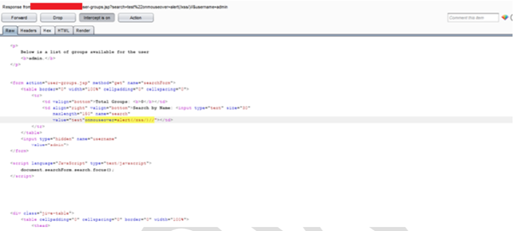
Figure 03: HTTP Response for the modified “search” variable with XSS payload.
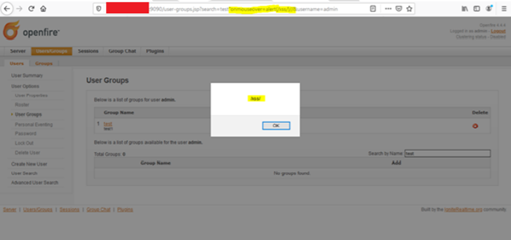
Figure 04: Injected XSS payload, “onmouseover=alert(/xss/)// gets reflected in the browser response.
Impact
- Stealing cookies
- End-user files disclosure.
- Redirection of the user to some other page or site.
Remediations
Perform context-sensitive encoding of untrusted input before it is echoed back to a browser by using an encoding library. Implement input validation for special characters on all the variables that are reflecting to the browser and storing it in the database. Implement client-side validation.
Timeline