Securin Zero-Days
CVE-2018-20432 - Hardcoded credentials in DLink CoVR-2600R Router
Description
The latest versions of the firmware have hardcoded default credentials that can be exploited by an unauthenticated attacker to gain privileged access to the firmware and to extract sensitive data.
Proof of Concept (POC):
Issues
1. Download the firmware from the mentioned download URLs.
2. Extract the firmware using binwalk. “binwalk -e COVR-3902_ROUTER_v101b05.bin.”
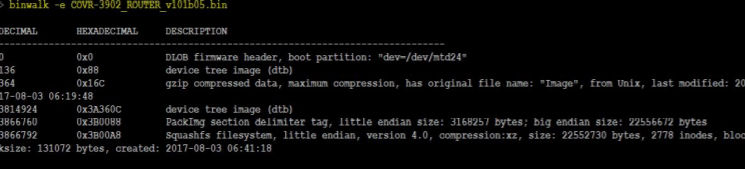
Figure 1: Extracting a firmware
3. Go to “cat ./etc/init0.d/S80telnetd.sh” to get a username
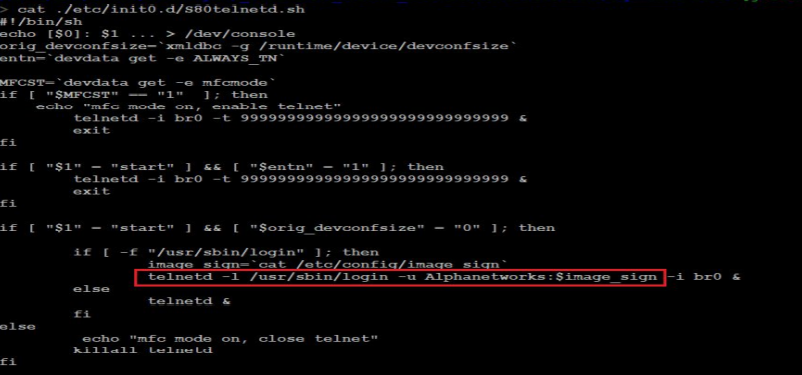
Figure 2: Clear text username as shown in screenshots
4. Go to “cat ./etc/config/image_sign” to get a password
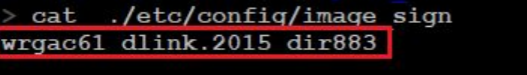
Figure 3: Clear text password as shown in screenshots
Username: Alphanetworks\
Password: wrgac61_dlink.2015_dir883
Impact
An unauthenticated attacker gains privileged access to the router, and to extract sensitive data or modify the configuration.
Remediations
Download and apply the relevant from the vendor:
Timeline